 Cyberattack is a new tool of national power. It provides a means of coercion, influence, and warfare. The use of cyber techniques as intelligence tools dates back to the 1980s; cyberattack by militaries dates back to the 1990s. Using cyber tools and techniques as an instrument of national power is the norm in the Gulf. The Gulf has become a flashpoint for cyber conflict given the high level of activity and the chance for miscalculation and escalation into conventional conflict.
Cyberattack is a new tool of national power. It provides a means of coercion, influence, and warfare. The use of cyber techniques as intelligence tools dates back to the 1980s; cyberattack by militaries dates back to the 1990s. Using cyber tools and techniques as an instrument of national power is the norm in the Gulf. The Gulf has become a flashpoint for cyber conflict given the high level of activity and the chance for miscalculation and escalation into conventional conflict.
The Gulf is unique in that the use of cyber techniques by governments for covert action is much more prevalent than in any region other than the Korean peninsula. The primary source of tension among Gulf states is the development by Iran of cyberattack capabilities that it has used and appears willing to use again. There is also a growing concern about Israeli cyber capabilities. This is an outgrowth of the larger disputes between Iran and Gulf Arab nations. Given the Gulf’s strategic and economic significance, cyber attacks that damage oil production or escalate into physical conflict could have global consequences. The use of cyber tools and the expansion of cyber capabilities could change the balance of military power among regional states and undermine Gulf stability, particularly if the Gulf Cooperation Council (GCC) states do not expand their defenses in response to this new threat and find ways to better cooperate.
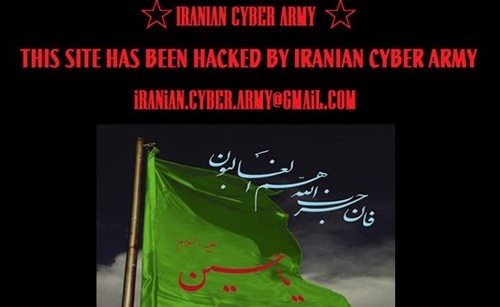
Three key incidents have focused the attention of Gulf states on cybersecurity. The first was the effect of social media and the Internet in the Arab uprisings of 2011 and the 2009 Iranian “Green Revolution.” The Internet can amplify political forces in ways that are difficult to predict or control. The second was the Stuxnet attacks launched against Iranian nuclear facilities in 2010. Stuxnet led to significant changes in Iranian policy, but it was not unique. Researchers around the world discovered significant malware programs—Stars, Duqu, Flame, Shamoon—used for espionage or attack against Gulf targets. Finally, the 2012 attacks on Saudi Aramco and the Qatari firm RasGas, generally attributed to Iran, put most Gulf countries on notice of the new kind of risk they faced.
In response to increased Iranian capabilities, the United States has begun to work with partner nations in the Gulf to improve their cyber defense capabilities. But almost all current “cyber powers” play some role in the Gulf. Israel
has a close and active interest in Iran, and Israeli sources report that Iran routinely probes Israel’s networks for vulnerabilities. Russia has worked with Iran in ways we do not fully understand and has sought to work with GCC states as well. There are reports that North Korea and Iran may be collaborating in developing cyberattack tools. . . .
Iran is far in the lead over the GCC states. Iran’s trajectory in developing cyber capabilities is a good example of how a medium-sized government willing to commit a relatively small amount of resources can build cyber power. Iran
sees cyberattack as another tool of its broader asymmetric warfare strategy for use against more powerful opponents. . . .
Iran and external actors like the United States, Israel, and Russia will continue to use cyber techniques for covert activities to achieve national goals. In the Gulf as in the rest of the world, cyberattack provides a new tool for nations to use in existing disputes.
James Andrew Lewis is a senior fellow and director of the Strategic Technologies Program at CSIS.
Image: Cybersecurity and Stability in the Gulf (graphic: PBS)