 The massive cyberattack that crippled public transportation, the central bank, government offices, the state power distributor, and public firms in Ukraine on June 27 serves as a potent reminder of the havoc that can be unleashed by low-level actors, according to an Atlantic Council analyst.
The massive cyberattack that crippled public transportation, the central bank, government offices, the state power distributor, and public firms in Ukraine on June 27 serves as a potent reminder of the havoc that can be unleashed by low-level actors, according to an Atlantic Council analyst.
“This is another reminder that low-capability actors can have a profound impact on critical infrastructure like media, finance, energy, and others,” said Beau Woods, deputy director of the Cyber Statecraft Initiative at the Atlantic Council’s Brent Scowcroft Center on International Security.
Besides Ukraine, which appears to have been hit particularly hard, symptoms of the attack were also reported from the United Kingdom, Russian oil producer Rosneft, Australia, the United States, India, and the Danish shipping company Maersk.
“Despite early indications, it’s unclear whether this attack was targeted against Ukraine or just happened to hit the news cycle there first,” said Woods.
Ukraine’s central bank said in a statement: “The National Bank of Ukraine has warned banks… about an external hacker attack on the websites of some Ukrainian banks.”
A spokesman for Ukraine’s presidential administration said it was paying “a high level of attention” to the situation.
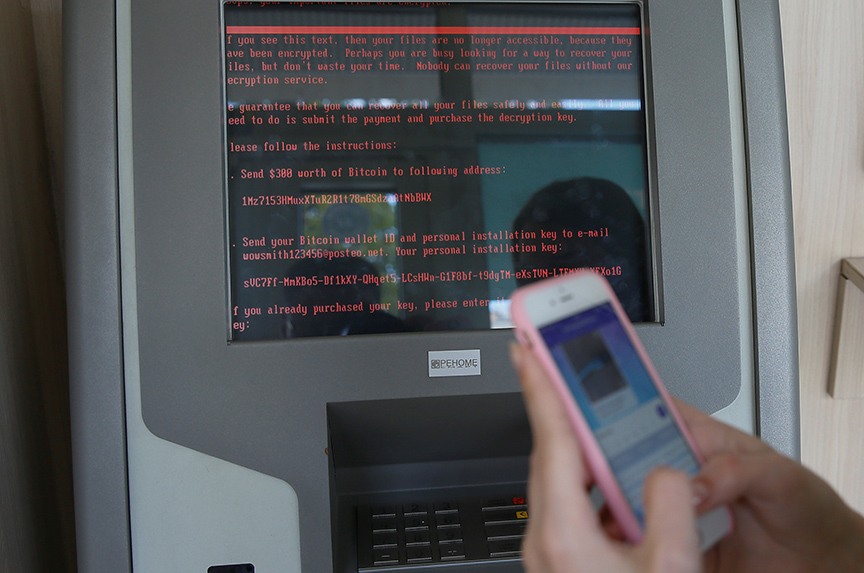
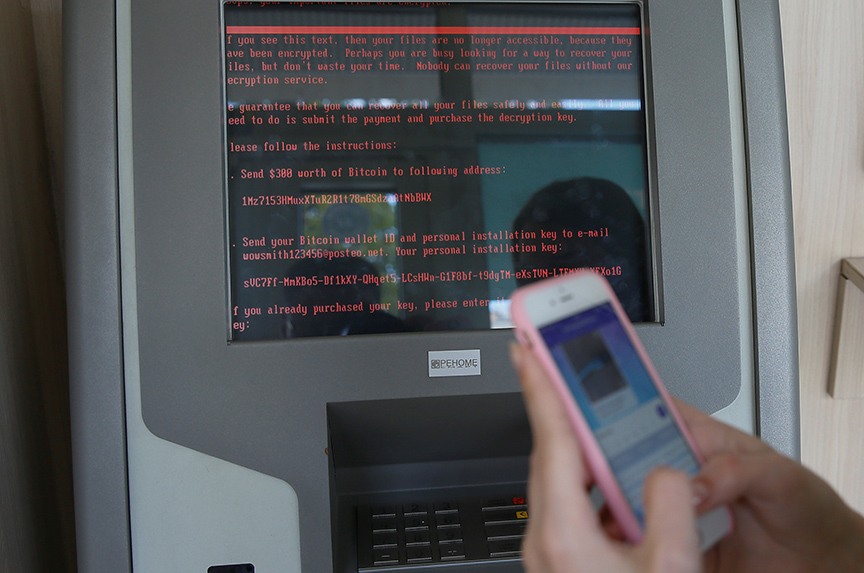
The virus used in the cyberattack is believed to be ransomware—malicious code that takes control of a computer system and demands ransom to fix the problem.
The virus was linked to malware called Petrwrap or Petya, which appeared to be derived from code developed by the US National Security Agency.
In April, a hacking group known as the Shadow Brokers released stolen software tools designed by the NSA to infect and control computers that use Microsoft Windows software.
The cyberattack unleashed on June 27 was the second in the past two months to be linked to the stolen NSA tools. An earlier attack in May crippled 200,000 computers in more than 150 countries. That attack involved ransomware, called WannaCry or WannaCrypt, and was believed to have been carried out by North Korea. In that attack, the malicious software, or malware, was transmitted via e-mail. Users who clicked on the e-mail found themselves locked out of their data and received ransom messages.
“This attack will be bigger than WannaCry if these attackers learned from earlier mistakes,” said Woods.
It remains unclear who is responsible for the more recent attack.
In the past, Ukrainian officials have blamed Russia, which has sophisticated cyber capabilities, for cyberattacks, including one on Ukraine’s power grid that left part of western Ukraine temporarily without electricity in December of 2015. A US Department of Homeland Security report concluded hackers were responsible for that outage, but did not ascribe blame.
In 2007, the tiny Baltic state of Estonia was the target of a massive cyberattack that was blamed on Russia.
Russia has also been accused by Western governments and intelligence agencies of meddling in US and European elections.
What can be done to protect against such attacks?
“Cyber hygiene isn’t just about patching faster, there are a number of sound cybersecurity practices that can blunt impacts from these types of events,” said Woods.
Ashish Kumar Sen is deputy director of communications at the Atlantic Council. You can follow him on Twitter @AshishSen.
Image: A message demanding money is seen on a monitor of a payment terminal at a branch of Ukraine’s state-owned bank, Oschadbank, in Kyiv, Ukraine, after Ukraine was hit by a wave of cyberattacks on June 27. (Reuters/Valentyn Ogirenko)