 Modern-day warfare is as much about cyberattacks and the protection of communication and information systems as it is about kinetic military action. In 2016, NATO’s institutional networks experienced on average 500 cyberattacks a month—an increase of roughly 60 percent from the year before. Other recent, high-profile, transnational cyberattacks, such as the WannaCry ransomware attack and Petya, highlight the urgent need for NATO and its member states to develop strong cybesecurity capabilities.
Modern-day warfare is as much about cyberattacks and the protection of communication and information systems as it is about kinetic military action. In 2016, NATO’s institutional networks experienced on average 500 cyberattacks a month—an increase of roughly 60 percent from the year before. Other recent, high-profile, transnational cyberattacks, such as the WannaCry ransomware attack and Petya, highlight the urgent need for NATO and its member states to develop strong cybesecurity capabilities.
Although NATO has been working toward a more comprehensive cybersecurity policy, there are two major challenges with its current strategy. The current plan places cyberattacks within the scope of Article 5 of the North Atlantic Treaty and the concept of collective defense, thus, creating high thresholds for engagement. In addition, it allows for mainly defensive and reactive measures, leaving less room for preventive or offensive operations.
NATO’s approach to cybersecurity can be traced back to early steps taken at the 2014 Wales Summit, in which NATO included cyber defense in its core tasks of collective defense. At the Warsaw Summit two years later, NATO recognized cyberspace as a “domain of operations,” reaffirming its defensive mandate with regard to cyber threats.
The Warsaw Summit Communiqué states that recognizing cyberspace as a domain of operations will “support NATO’s broader deterrence [of] and defense [against cyber threats],” and NATO promised to continue integrating cyber defense “into operational planning [to ensure] a better management of resources, skills, and capabilities.”
Armed attack-threshold
The designation of cyberspace as a domain of operations has far-reaching implications. As decided upon by Allied countries in the Tallinn Manual 2.0, such a label allows NATO to act only against those cyberattacks that qualify as an “armed attack.” In the case of cyberattacks, however, opponents often do not seek physical destruction. Of late, cyberattacks have moved further away from traditional warfare in pursuit of subtler influences, sometimes involving coercive political pressure. On July 28, the US Congress voted for new sanctions on Russia for its meddling in the 2016 US presidential election in favor of then-candidate US President Donald J. Trump.
By placing cyberattacks within the doctrine of collective defense, NATO limits its response to those cyberattacks that reach the armed-attack threshold, making it extremely difficult for NATO members to effectively address cyberattacks that do not qualify as such.
Whether a cyber operation constitutes an “armed attack” also depends on the parties involved. Traditionally, the right to collective defense could only be invoked in case of an armed attack undertaken by one state against another. NATO’s Strategic Concept allowed for a wider definition, stipulating that “the North Atlantic Treaty covers any armed attack on the territory of the Allies, from whatever direction or source.” Although this allows NATO to take defensive action against cyberattacks carried out by non-state actors, there is still some uncertainty within the community of allied countries as to when collective defense against non-state actors is permissible. One of the biggest challenges in this case remains attribution. It is often difficult to trace cyberattacks back to one specific organization.
From defensive to offensive capabilities
Currently, NATO’s cybersecurity strategy is strictly defensive. The NATO Computer Incident Response Capability (NCIRC) protects NATO’s own networks, and NATO supports allied members in their individual cyber defenses through intelligence gathering and sharing, the employment of high-readiness cyber defense teams, the development of targets for allied countries to facilitate national cyber defense capabilities, and investment in education, training, and exercise.
As James A. Lewis, director of the Strategic Technologies Program at the Center for Strategic and International Studies, wrote for the Tallinn Papers, a series of publications from the NATO Cooperative Cyber Defence Centre of Excellence, “a cyber defensive orientation is the equivalent of a static defense, defending fixed positions rather than maneuvering, and conceding initiative to opponents.”
Defensive measures might hold off an individual cyberattack, but they do not address the underlying threat. Although the protection of NATO members’ national networks should be a priority, the most effective way to provide sustainable and long-term protection against cyberattacks is through offensive capabilities and the destruction of opponent networks and systems.
While individual member states can take certain steps toward achieving this objective—the United States, for example, has already employed strong offensive cyber capabilities, such as Stuxnet—a collective NATO doctrine would provide allied countries with the necessary guidelines regarding proportionality and subsidiarity when employing offensive cyber capabilities. NATO’s cybersecurity policy should provide a clear framework to address the relatively uncharted territory of offensive cyber operations.
Recommendations
Current developments in the field of cybersecurity require a more proactive approach. In order to counter cyber threats, NATO should pursue a broader and more dynamic operational framework than that of collective defense. As the cyber capabilities of NATO’s opponents grow more sophisticated, the Alliance should adopt a cybersecurity policy that can effectively counter these threats.
Primarily, this means that NATO should create a public doctrine, independent from the concept of collective defense, that allows member states to not only act defensively, but also offensively. Second, NATO should pursue a public policy that also effectively addresses cyber threats that stay below the armed attack-threshold. Overcoming these two challenges would enable the community of Allied countries to develop the necessary framework to comprehensively address current cybersecurity threats.
Barbara Roggeveen is a research assistant at the Slavic Department of the University of Amsterdam and a former intern with the Atlantic Council’s Dinu Patriciu Eurasia Center.
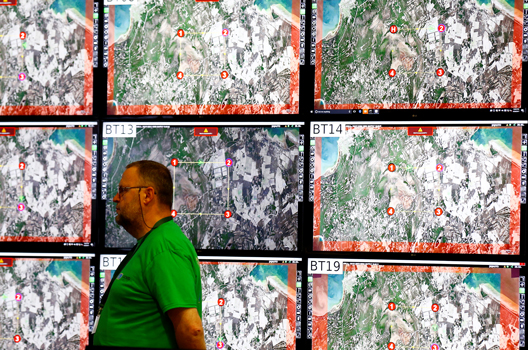
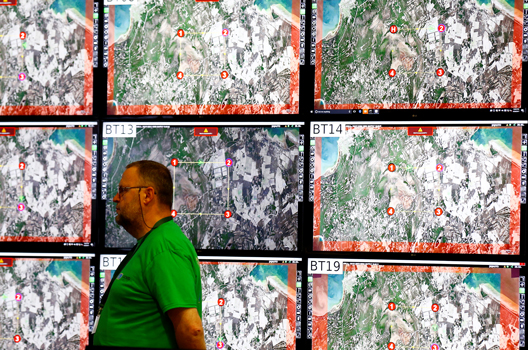
Image: A man stands next to screens during the Locked Shields 2017 exercise organized by NATO Cooperative Cyber Defence Centre of Excellence in Tallinn, Estonia, April 26, 2017. (REUTERS/Ints Kalnins)