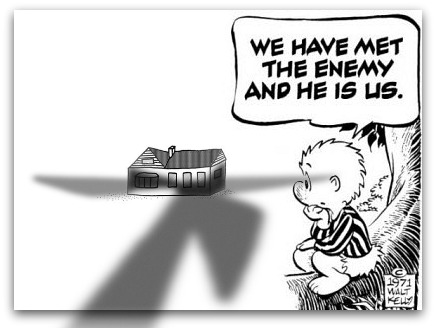
From Jason Healey, the New Atlanticist: The United States government has apparently struck a blow against the Iranian nuclear enrichment capability by using Stuxnet to disable centrifuges. While this cyber weapon destroyed centrifuges and seized up the enrichment process, the cost in American cyber power ultimately will not have been worth these limited gains. . . .
[N]ow that this genie is out of the bottle, the United States will be blamed for every piece of sophisticated malware from now on. Other nations and non-state criminals will get free passes – they conduct attacks too, but we’re the ones that got caught.
The most important reasons why Stuxnets are not in US interests revolve around the basic argument that “those with glass industrial control systems should not throw stones.” The United States has incredibly vulnerable cyber systems, including in critical infrastructures like the electrical generation and transmission systems. Not only has the United States legitimized attacks against these systems, they are now likely open to direct reprisal from Iran.
DHS officials have testified to Congress they are “concerned that attackers could use the increasingly public information about [Stuxnet] to develop variants targeted at broader installations of programmable equipment in control systems.” General Alexander of US Cyber Command similarly told lawmakers that “Attacks [such as Stuxnet] that can destroy equipment are on the horizon, and we have to be prepared for them.” The government has been clear about the proper response to Stuxnet and other threats with Alexander writing to Congress that “Recent events have shown that a purely voluntary and market driven system is not sufficient. Some minimum security requirements will be necessary” using regulation to secure critical infrastructure. . . .
If Obama was speaking the truth when he said “America’s economic prosperity in the 21st century will depend on cybersecurity” then it is unlikely Stuxnet is in our long-term interest. It slowed the Iranian nuclear program down, but does not seem to have caused extended disruption; it was, therefore, a tactical rather than a strategic win. Unfortunately, it may have torpedoed American credibility on all future cyber issues and could be remembered as the equivalent of the invasion of Iraq: a mistaken use of force against weapons of mass destruction. Ultimately it may help deliver a strategic loss to the United States. Rather than seen as inventing and nurturing cyberspace, we may seem to digital natives as a crotchety old man, a declining imperial power lashing out as the domain of its own making slips ever more out of its influence.
The United States has now made the “demonstration” attack that some in Washington DC believe is needed to deter our adversaries. As General Cartwright expressed, “You can’t have something that’s a secret be a deterrent. Because if you don’t know it’s there, it doesn’t scare you.”
With Stuxnet, we now have other nations scared of us in cyberspace. Perhaps, like General Cartwright wants, this will be for the best … but like so much else in cyberspace, this answer is still to be discovered.
Jason Healey is the Director of the Cyber Statecraft Initiative at the Atlantic Council of the United States. You can follow his comments on cyber cooperation, conflict and competition on Twitter, @Jason_Healey.
Image: pogo-we-have-met-the-enemy.jpg