 In December of 2015, a sophisticated cyberattack on Ukraine’s power grid caused outages that left nearly 225,000 citizens without power. The malicious software used in the attack was traced back to Russian groups, making the intrusion a stunning realization of the threat posed by cyberattacks. Though this event called attention to the vulnerability of European cyber defenses, the European Union has done little to adopt a more unified cybersecurity policy for its energy infrastructure. The EU needs to reinforce cybersecurity defense measures in tandem with implementing a more integrated energy policy. Understanding the rise of complex terror attacks on European soil and the use of cyberattacks as a tactic, cybersecurity and dedicated critical infrastructure protection need to constitute larger parts of the EU’s plans for further energy integration.
In December of 2015, a sophisticated cyberattack on Ukraine’s power grid caused outages that left nearly 225,000 citizens without power. The malicious software used in the attack was traced back to Russian groups, making the intrusion a stunning realization of the threat posed by cyberattacks. Though this event called attention to the vulnerability of European cyber defenses, the European Union has done little to adopt a more unified cybersecurity policy for its energy infrastructure. The EU needs to reinforce cybersecurity defense measures in tandem with implementing a more integrated energy policy. Understanding the rise of complex terror attacks on European soil and the use of cyberattacks as a tactic, cybersecurity and dedicated critical infrastructure protection need to constitute larger parts of the EU’s plans for further energy integration.
The attack on Ukraine’s grid shows how such complex intrusions pose a major threat to energy security in the EU. Both state and non-state actors have developed greater cyber capacity, enlarging the field of potential enemies. For many years, only a few countries—the United States, China, and Russia—were capable of carrying out disabling cyberattacks on computerized infrastructure, making any attack easily traceable to its perpetrator. As these capabilities are developed by an increasing number of countries, the range of threats have increased and the difficulty of ascribing blame has risen. Non-state actors—particularly terrorist organizations—have significant interest in executing cyberattacks in Europe. Currently, these groups have little ability to do so. Federal Bureau of Investigation Section Chief John Riggi noted their position as having “strong intent [with] low capability.” For now, these types of attacks have been mostly foiled, but with an increase in the number of attempts and the rise of more tech-savvy terrorist groups such as the Islamic State of Iraq and al-Sham (ISIS), concerns rise about the potential for terrorist groups to develop or buy sophisticated cyberattack ability.
The European Commission convened the second Energy Infrastructure Forum on June 23—its first since the cyberattack in Ukraine in December. The forum set out to increase integration of regional security networks across the energy industry. Such integration is far overdue. While the EU was borne out of a need for energy coordination, it has since abandoned these origins to the detriment of its very security. Its lofty aims of collectively ensured energy security have been crippled by its founding treaty, which guarantees states the right to self-determination of energy makeup—resulting in a scattered energy policy complete with a patchwork of regulations and strategies that are vulnerable to change based on member state politics. This hampers the bloc’s ability to diversify its energy sources, balance demand and supply across the Continent, and leaves major vulnerabilities open in the security structures protecting its energy infrastructure.
Outside of the Forum, the EU has taken some steps toward increasing collective cybersecurity. The EU’s Programme for Critical Infrastructure Protection (EPICIP) was enacted in 2007, spurring a series of projects and assessments to evaluate the security of the transnational electric grid and gas network. Several parts of the Program have involved cybersecurity, including the Thematic Network and the Critical Warning Information Network, which are structured to facilitate the exchange of information regarding threat assessment and risk management.
By 2018, the European Commission plans to launch two new initiatives—the Network and Information Security (NIS) Directive and the General Data Protection Regulation (GDPR)—which together aim to force energy operators to adhere to certain requirements of security and reporting and to protect critical data.
Even so, the EU must do more to develop a holistic plan for critical infrastructure protection. It needs greater integration to ensure uniformity in security policies and greater intelligence sharing on cybersecurity threats. It can look toward NATO, with which it is building a relationship of data and best practices exchange. NATO is deeply involved in European cyber defense and has demonstrated concern about the growing number of attacks on critical infrastructure. In 2014, NATO enacted a cyber defense policy that cemented cyber defense as a critical component of its mission of “collective defense” and committed to integrating it into its security efforts at-large.
The NATO Defense Planning Process, which will enter into force in 2017, sets ambitious cyber capability targets for the Alliance’s member states. Adopting more of these measures of capability targets and placing greater emphasis on a uniform policy will help the EU secure its vulnerable infrastructure. Moving forward, the European Commission must prioritize these measures as an integral component of its broader plans for energy integration and uniformity.
Madison Freeman is an intern with the Atlantic Council’s Eurasian Energy Futures Initiative.
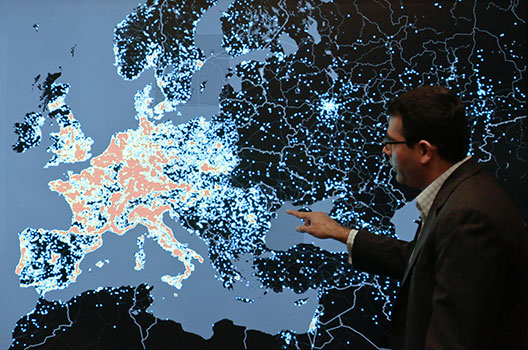
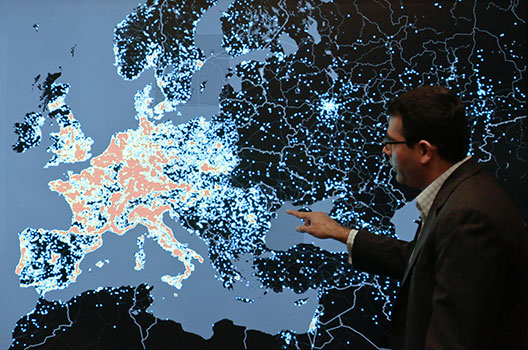
Image: Vishant Patel, senior manager of investigations at the Microsoft Digital Crimes Unit, shows a heat map and talks about how malicious computer networks known as the Citadel Botnets attack computers in Western Europe at the Microsoft Cybercrime Center in Redmond, Washington November 11, 2013. (REUTERS/Jason Redmond)