The 5×5—A cyber wish list at a ‘moment of reckoning’

The recent SUNBURST compromise of numerous government and private sector company networks has led some, including Microsoft President Brad Smith, to dub the incident a “moment of reckoning.” It is a sign that the US government may need to rethink its approach to cybersecurity and implement sweeping reforms. The development only adds urgency to this year’s National Defense Authorization Act, which includes twenty-six legislative recommendations from the Cyberspace Solarium Commission’s final report to improve the United States’ cybersecurity posture. The act is currently awaiting signature on US President Donald J. Trump’s desk.
The Trump administration recently proposed splitting the “dual hat” leadership arrangement of the National Security Agency and US Cyber Command, while the Solarium Commission’s congressional leaders have unanimously pushed back against the idea. But there are plenty of other ideas out there for improving US cybersecurity. Below, our Cyber Statecraft Initiative experts reveal their own cyber wish lists during this holiday season.
#1 What is the one cybersecurity issue that too few people are paying attention to, but everyone should be watching?
Sherman Chu, cyber intelligence analyst, NYC Cyber Command:
“The potential rise of advanced cyber ‘mercenary groups’ that would operate for any nation-state or other entities indiscriminately. Infosec discussions are full of ‘likely state-sponsored’ actors or contractors tasked by governments. The potential rise of mercenaries (such as the one mentioned by Kaspersky’s report on DeathStalker) can complicate the prognosis of targeting and attribution effort.”
Kurt John, chief cybersecurity officer, Siemens USA:
“The security of manufacturing facilities. The global pandemic exposed vulnerabilities in a highly concentrated supply chain, and while I don’t think companies are going to leave China, particularly if goods they produce are popular in that market, I do think that there will be a diversification of their supply chain—to increase localization and resilience. And when this happens, this newly diversified supply chain will need to get security right. Otherwise, a highly concentrated but easier to secure supply chain will become decentralized and more expensive to retroactively fix.”
Katie Nickels, director of intelligence, Red Canary:
“Business Email Compromise (BEC), which is a method of compromise in which adversaries trick users into transmitting money to them via email communications. The Federal Bureau of Investigation’s (FBI) Internet Cyber Crime Center report from last year shows the losses from BEC were many times that of ransomware, and this year will likely be no different. One of the challenges of BEC is that it’s not just a technical problem to solve—it’s also a matter of implementing secure company policies on transferring money and security-awareness training, making it a problem that some cybersecurity practitioners overlook.”
Justin Sherman, fellow, Cyber Statecraft Initiative:
“The United States’ lack of robust citizen and consumer privacy protections as a security issue—how it enables all kinds of malicious and harmful behavior, from internet microtargeting to the threats to democracy perpetuated by the data-brokerage industry.”
Camille Stewart, cyber fellow, Harvard Belfer Center:
“Technology and software supply-chain security is an issue that impacts so much. Creating standards and policy that will incentivize and, in many cases, require transparency into our supply chain would provide industry and government alike the insight to more proactively mitigate vulnerabilities and attacks on infrastructure—critical and otherwise. This need is underscored by a recently detected software supply-chain compromise and the related post-intrusion activity affecting multiple entities worldwide.”
#2 It’s January 21: President-elect Joe Biden’s administration has just stepped through the looking glass with the first Zoom inauguration. What is the first thing the administration should do in cybersecurity policy?
Chu: “The Biden-Harris administration should appoint a national cyber director as mentioned in the Cyberspace Solarium Commission report. There is a critical need for a person to coordinate, support, and deconflict cybersecurity efforts between the many executive branch agencies.”
John: “A holistic federal approach to cybersecurity that ties together the core principles needed to help keep us protected as a nation. Currently there are fifty different approaches with various priorities, not including specific topics within the field of cybersecurity such as the Internet of Things (IoT). Individual state approaches are better than nothing, but hey—this is my wish list, so I hope a unified federal approach will be forthcoming.”
Nickels: “The first thing the new administration should focus on is strengthening public-private partnerships and information sharing. Information sharing is a crucial way that cybersecurity practitioners succeed at their jobs, but currently much of the most successful information sharing and collaboration is informal. The new administration could strengthen public-private information sharing by implementing existing recommendations such as those from the Cyberspace Solarium Commission. Protections for private-sector organizations sharing information with the government will be key, as some organizations may hesitate to share with the government unless they can ensure that they are not opening themselves up to legal challenges.”
Sherman: “The administration needs to reinstate some kind of White House cyber coordinator. The Trump administration has done a lot of damage across traditional policy and diplomatic areas that intersect with tech (such as deteriorating alliances and undermining US global credibility) as well as on technology-policy topics specifically (such as lowering the importance of the US State Department’s cyber office and eliminating the White House cyber coordinator role in the first place). Having a person at the White House specifically working to repair the damage and advance new policies will be critical.”
Stewart: “Either rewrite the cyber strategy or create an implementation plan that includes the Cyber Solarium recommendations so the interagency has a direction and a mandate.”
#3 What is one thing you wish policymakers in your country or community would do differently or get right?
Chu: “The Federal government should further empower state, local, tribal, and territorial (SLTT) cybersecurity efforts by providing additional funding and expanding grounds for collaboration/cooperation between individual entities within the sector. The Center for Internet Security’s Multi-State Information Sharing and Analysis Center (MS-ISAC) is a good start, but collaboration between SLTT entities is still nascent and a consolidated view into the threat landscape targeting SLTT is disparate.”
John: “Particularly at the local community level, I would love to see cybersecurity be more democratized into ongoing policy adjustments as well as new policies.”
Nickels: “I wish policymakers would realize that cybersecurity is an ongoing challenge that cannot be fixed with any single piece of legislation or new agency. We will never be able to prevent every cyber intrusion, so instead as a country we must focus on enabling practitioners to prevent, detect, and respond to intrusions quickly and efficiently. Cybersecurity will be a challenge that we continue to grapple with locally, nationally, and globally for years to come.”
Sherman: “Stop framing a range of technology-policy issues in zero-sum terms or as false dichotomies. Artificial-intelligence research writ large is not an “arms race”; regulating corporate-data collection with privacy laws is not a matter of choosing between regulating US companies or competing with Chinese tech firms. Key to developing coherent and effective technology policy in today’s world is understanding the interconnection, interdependence, and areas of gray at play, but putting everything in zero-sum terms or accepting framings of the issues that are in fact false dichotomies only undermines that effort.”
Stewart: “Understanding how social-justice issues, especially racism, affect the formation and efficacy of technology and cybersecurity policy and controls. Racism and bigotry are being weaponized against us and will continue to be our Achilles heel.”
More from the Cyber Statecraft Initiative:
#4 What is one small action that you wish the average user would take in their daily approach to cybersecurity that could have a big impact on the security of society?
Chu: “If the average user employs the use of multi-factor authentication (MFA) for their emails and devices, we will definitely see a dramatic decrease in incidents.”
John: “Turn on two-factor authentication on all accounts. It’s like in any sport, foundational activities—the basic blocking and tackling—go a long way to help keep us protected.”
Nickels: “I wish the average user would update their software and devices as soon as possible. Updates fix the security issues that software and hardware providers know about. While updates can get annoying, these updates give users a chance to decrease the likelihood of adversaries compromising their systems. I wish the average user would treat updating like brushing their teeth.”
Sherman: “Turn on two-factor authentication.”
Stewart: “Be intentional about the access to data and systems granted to applications and services. I want users to make informed and intentional risk calculations with their digital security and privacy just as they do with their physical security.”
#5 What is the most overblown cybersecurity issue that you wish people would spend less time worrying about?
Chu: “News and discussion on nation-state threat actors overshadow the need to address malspams and BEC campaigns. Analogically, we should worry about robbers who are trying to smash through our windows every day before we worry about foreign-nation operators trying to sabotage our house.”
John: “Nothing. There is a sliding scale of priorities given some external factors. For now, the environment is such that this scale is shifting much more than usual so we should all be paying attention and be ready to adjust accordingly.”
Nickels: “While I realize the irony of saying this in the midst of a suspected state-sponsored global supply-chain compromise, I think the focus on advanced persistent threats (APTs) is overblown. For the average non-governmental organization, crimeware and ransomware is more likely to impact their networks than state-sponsored APT activity. Even as the recent SolarWinds compromise was breaking, criminal actors and ransomware operators continued their operations. Focusing on those threats may be less ‘exciting,’ but it’s often more important for the average organization.”
Sherman: “I’ll cheat in my response here and answer in a slightly different way. I don’t want to say the threat of Russian election interference is ‘overblown,’ because it’s very real and very serious (and still downplayed by many elected officials), and I don’t believe we should stop worrying about it. But I do think the fixation on election misinformation and disinformation from Russia in the past couple of years has led many people astray from a broader conversation (of which Russia is one component) about the place of truth in the modern information ecosystem; systemic problems with social-media platforms and not just with malicious foreign actors; and the extent to which domestic actors, and actors beyond Russia, also can and do spread election mis- and disinformation as well.”
Stewart: “The notion that people are the weakest link. Cybersecurity is a human-centered challenge and if we focus more on meeting people where they are while educating them to elevate their understanding, we, as practitioners, would be a lot more successful.”
Simon Handler is the assistant director of the Atlantic Council’s Cyber Statecraft Initiative under the Scowcroft Center for Strategy and Security, focused on the nexus of geopolitics and international security with cyberspace. He is a former special assistant in the United States Senate. Follow him on Twitter @SimonPHandler.
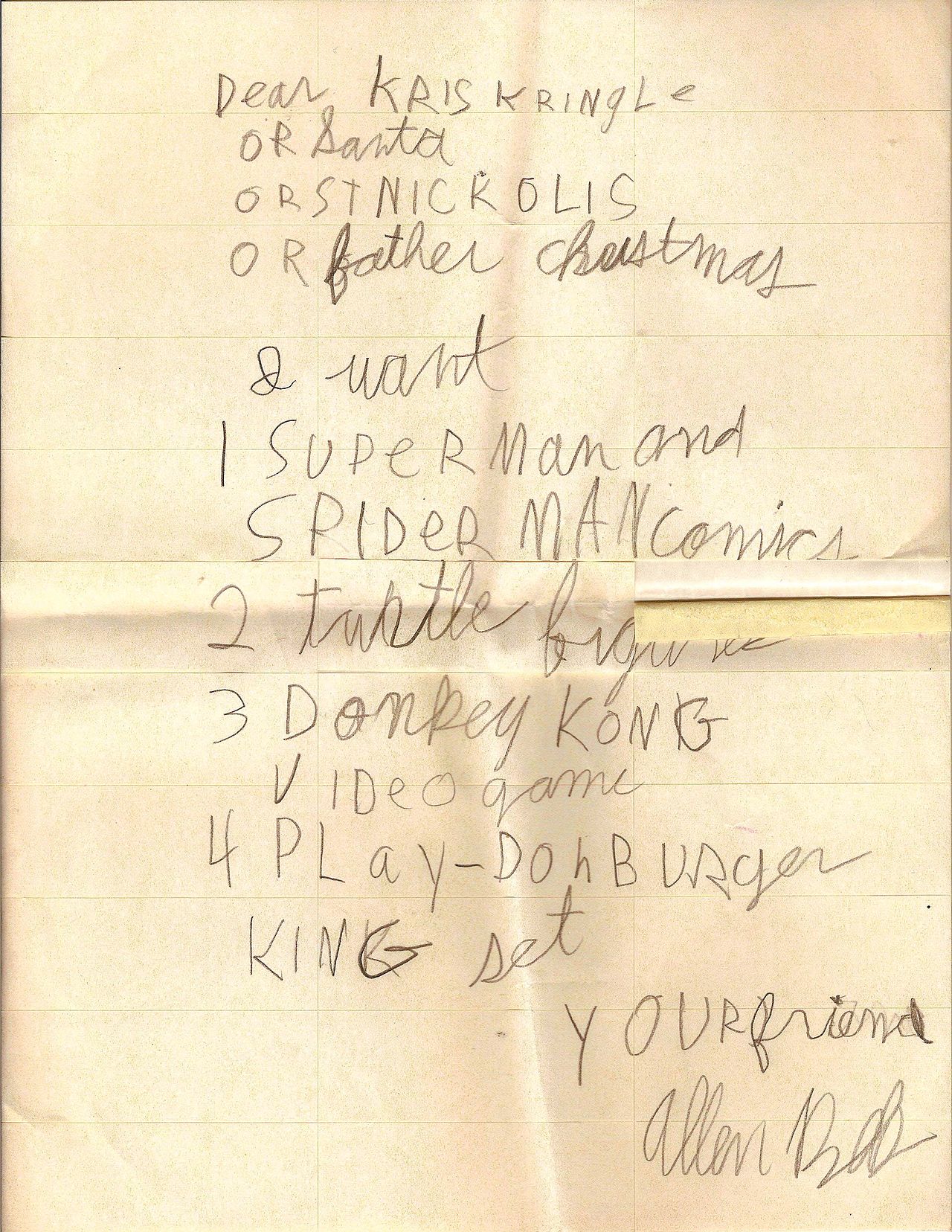
Image: Image source: Valerie's Genealogy Photos/Flickr