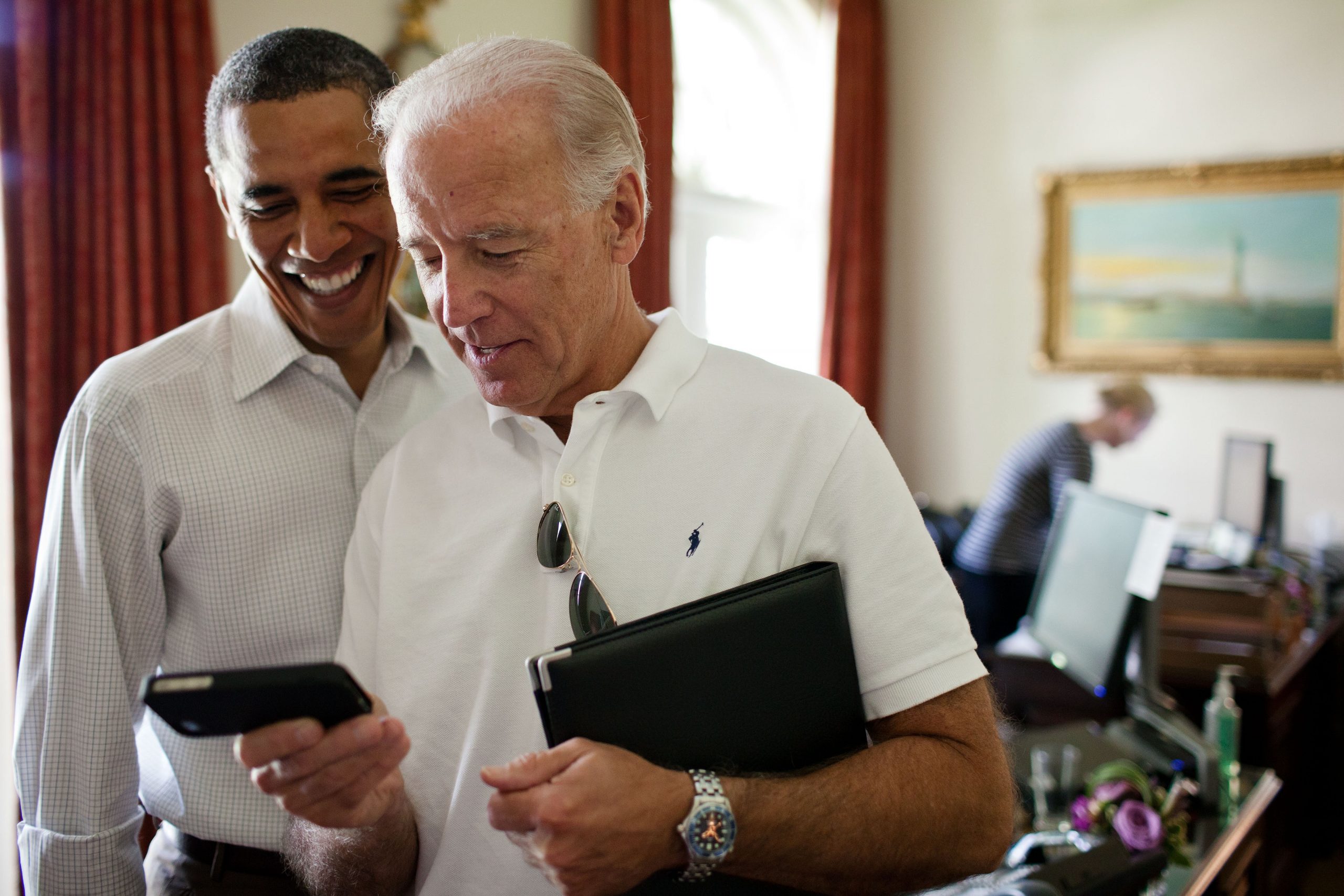
The 5×5—Looking ahead for the Biden administration after a busy year in cybersecurity

It’s been a wild twelve months in the world of cybersecurity since the Atlantic Council’s Cyber Statecraft Initiative (CSI) launched the 5×5 series. In March 2020, the Cyberspace Solarium Commission released a report in which it mentioned the word “resilience” 121 times, highlighting the rising importance of creating resilient systems to defend cyberspace. The Commission also issued a white paper on Growing a Stronger Federal Cyber Workforce, outlining recommendations to overcome the US government’s cyber workforce shortage. In November, Amazon Web Services added a small amount of capacity to its servers, leading to a widespread outage that impacted thousands of services. In December a threat intelligence company discovered that a Russian-linked hacking group leveraged a software supply chain vulnerability to breach roughly a dozen US government agencies—as far as we know—as well as countless private-sector organizations in a potentially once-in-a-generation cyber incident. And, to round things out, former US President Donald Trump’s administration dropped its National Maritime Cybersecurity Plan, outlining policies to mitigate risks to the sector, a mere two weeks before leaving office.
CSI has been busy trying to keep up. Our How Do You Fix A Flying Computer? report provided a framework for defense organizations to build and maintain resilient software-intensive mission systems. We held four completely virtual Cyber 9/12 Strategy Challenge competitions, aimed at developing the next generation of talent to tackle the most pressing cyber policy challenges. We published two reports as part of our cloud security & policy practice area. We launched Breaking Trust, a project that catalogued a decade’s worth of software supply chain compromises and proposed recommendations on how to address gaps in security. And we convened key stakeholders from the public and private sectors to improve cybersecurity and cooperation across the maritime sector.
We’re looking forward to building on our resilience, education/workforce, cloud computing, supply chain, and maritime cybersecurity work in 2021. For the one-year anniversary edition of the 5×5, we brought together a group of experts, each focused on a different area of our work, to ask them about what’s to come in the year ahead.
#1 If you had to give one “A” grade and one “F” grade to two cybersecurity policies developed by the past administration, which would you choose?
Xavier Bellekens, lecture-chancellor’s fellow, Department of Electronic and Electrical Engineering at the University of Strathclyde:
“The creation of the Cybersecurity and Infrastructure Agency (CISA) is a major advancement in the area and I would certainly rate that as an ‘A.’ However, the Trump administration has also tremendously weakened the cybersecurity effort by not making cybersecurity one of the top priorities of the mandate, by claiming election fraud through unproven compromises of the voting system, or by terminating Christopher Krebs while he was the CISA Director.”
Trey Herr, director, Cyber Statecraft Initiative:
“Big swing and a miss by the Trump administration on its last-minute executive order to develop know-your-customer requirements for cloud (Infrastructure as a Service) vendors. The policy slid sideways and sloppily into an important issue in the abuse of cloud services by state and criminal actors. An ‘F’ for timing and glaring substantive gaps.
On a more positive note, the US Department of Homeland Security’s (DHS) CISA gets a solid ‘A’ for its new effort to bring in credible members of the cybersecurity community as visiting researchers and government experts to help with Operation Warp Speed and to bridge the policy-researcher divide in support of other pockets of excellence in CISA and across US government cyber policy.”
JC Herz, chief operating officer, Ion Channel; fellow, National Security Institute:
“A+ to the US Food and Drug administration’s (FDA) regulatory guidance requiring a software bill of materials (SBOM) for medical devices as a condition of FDA approval, and to the Department of Commerce National Telecommunications and Information Administration’s (NTIA) Software Component Transparency multi-stakeholder initiative which informed this.
An ‘F’ goes to government agency provisions of cybersecurity testing tools that aren’t ready for prime time and aren’t actively maintained. Both CISA and the National Institute of Standards and Technology made contractor-developed cybersecurity and/or supply chain interdependency assessment tools available as binary downloads from a federal web site. Both those tools are themselves horrendously vulnerable. Both agencies have been informed of the findings and have done nothing to remediate the vulnerabilities in their own cyber-assessment tools. That makes the federal government a risky software supplier and possible vector for attack…of the entities it’s regulating and dictating standards to.
Both the ‘A’s’ and the ‘F’s’ boil down to one theme: Lead by example.”
Reed Porada, security researcher and instructor, Boston Cybernetics Institute:
“I think Cybersecurity Maturity Model Certification (CMMC) is the main ‘policy’ change that I can think of from the last administration. I would put this somewhere towards a ‘C,’ maybe leaning towards a ‘D.’ While I think the intent is good, I am not confident that the results will lead to real systemic change. I feel that the policy is perpetuating a compliance culture, and not going to lead to large changes in our postures. Take the SolarWinds hack as an example. Many of the companies that were impacted by that attack likely were considered to have level four or higher processes and practices on the five-level maturity model. Yet they were still unknowingly compromised for a substantial time. Furthermore, I am not sure the responses to the breach are necessarily transformative. CMMC does not really push for thinking differently or owning the problem.”
Safa Shahwan Edwards, deputy director, Cyber Statecraft Initiative:
“I would grade Executive Order 13870 here. Leveraging the National Initiative for Cybersecurity Education (NICE) Framework to clarify what cyber skills are needed for federal positions, as well as streamlining the taxonomy used, gets an A. This makes it easier for the federal government to communicate what it needs in terms of cyber talent and, in turn, makes it less daunting for prospective applicants to consider applying for a cyber position, hopefully alleviating the government’s cyber skills shortage. On the other hand, there’s a dire need for multidisciplinary talent in the federal government to address tomorrow’s cybersecurity challenges—whether they be related to strategic communications, law, geopolitics, or other topics. In the executive order, much focus remained on the development and acquisition of hard technical talent so it also gets an ‘F.’”
#2 What phenomenon in your area of focus will require the most attention from the new administration?
Bellekens: “Cyber attacks are on the rise in the maritime industry and a successful attack could potentially impact the whole supply chain. It is therefore key to evaluate the resilience of the maritime and supply chain industries against foreign threats and build resilience at its core.”
Herr: “Every day brings new and diverse ways to use software, yet the way we manage risk in the software supply chain has continued to evolve slowly. That mismatch bit hard in 2019 and 2020 and the resulting Sunburst crisis continues to reveal new shades of awful in how private sector companies build and secure their products and how the government tries to certify and buy them. This will keep happening unless we stop trying to certify and secure all products equally, reinvigorate the local decision-making and information sharing authorities of defenders, and better tie investments and certification of new technologies to insights into adversaries gleaned from offensive activity and intelligence collection. Not a little nudge to bring defense and offense closer semantically, but a significant cultural shift in how we develop offensive plans and priorities informed by a self-aware defense and ground-up change to how we make defensive investments informed by offense.”
Herz: “How to raise security posture without heavyweight and labor-intensive control regimes that can only be staffed and executed by a dwindling and behind-the-curve defense industrial base. If a cybersecurity measure is not automatable, it’s not real. If it can’t run at scale, it’s a science project with no business relevance.
Also, for the love of God, be cognizant that smart cities and green anything create a vast new attack surface. For new systems, the cybersecurity and verifiable ongoing assurance bar should be an order of magnitude higher than for legacy, unless you’re interested in having power and transportation systems blacked out by the next SolarWinds. Municipalities all want the sizzle of being a smart city but are in no way staffed to assure vendor solutions or integrator deliverables. They actually trust vendors and global consultants to assure their systems on an ongoing basis, which is heartbreaking.”
Porada: “Ownership of the cybersecurity problem. What I mean by that is that we cannot keep looking towards technology or industry to solve our security problems. We have to own our security risks as a government and actively manage those risks and our technical baselines. This also means communicating up the chain when we do not have the capacity to manage the risk. Instead of pushing issues to the next ‘block’ for an acquisition, or to a plan of action and milestones (POAM) to only get kicked down the road, we need to actively communicate the needs, risks, and priorities.”
Shahwan Edwards: “The Biden administration will need to devote time and resources to cyber capacity building. There may be a new president in town, but the United States’ shortage of cybersecurity talent (exacerbated by the pandemic) remains. The new administration won’t have the luxury of addressing just today’s cybersecurity challenges and they’ll need to get serious about workforce development and getting more people into the cyber talent pipeline—and that will mean more nontraditional candidates.”
More from the Cyber Statecraft Initiative:
#3 As the Biden administration embarks, where are the best opportunities for near-term cybersecurity progress?
Bellekens: “In the maritime sector, the new administration has an opportunity to shape the future of threat intelligence and information-sharing across actors, learn from other critical national infrastructures that have undergone a digital transformation, and increase the nation’s cyber workforce in the sector. These measures would, in turn, increase the resilience of the maritime industry.”
Herr: “The creation of the national cyber director is an overdue opportunity to bring deep substantive expertise to the creation and implementation of the next national cybersecurity strategy. The office can provide a clear and senior voice advancing an operational public-private partnership in cybersecurity and help to better blend insights about adversary capabilities and intentions with defensive investments and architectural choices. A new office of this size and seniority is a chance to inject significant cultural reform into the US cybersecurity strategy development and policy coordination mechanism. Absent an immediate blunder, like dual-hatting the role under an existing policy shop, the administration has little but potential here.”
Herz: “Double down on supply chain and software inventory transparency: if agencies and regulated enterprises don’t know what they’re running and don’t measure how long it takes to locate and remediate issues, there’s no way they can manage cyber risk. SBOM should be required for any software procured by the federal government and for software consumed by entities regulated by CISA. The FDA has already broken ground on the regulatory front. Regulated enterprises in energy, automotive, and other sectors are doing proofs-of-concept. The NTIA’s multi-stakeholder, public-private proof-of-concept model seems to work ten times as effectively as any task force or federally funded research and development center-led effort, because forward-leaning, large-scale, and private-sector entities in finance, healthcare, manufacturing, energy, and other critical infrastructure domains are driving results that are facilitated by informed policy people (i.e. Allan Friedman). Learn from this model, support it, and scale it.”
Porada: “I don’t know that I have a thought on a quick win. Although, maybe there is a way to create or set a policy to shape future systems development. Many of our legacy systems will be stuck in legacy acquisition and operations processes for the rest of their useful lifetimes. Can we do better with new starts in the near term?”
Shahwan Edwards: “Near term, the new administration can kill two birds with one stone leveraging the State Department’s shiny new cyber bureau to continue collaboration with international partners and foreign governments on cyber capacity building. The State Department has a track record in this space and has supported foreign governments in developing secure, open, and resilient cyber ecosystems. Through this, the United States can continue to secure weak links in cyberspace, bolster international partnerships, and continue to strengthen cyber diplomacy.”
#4 Where are we most likely to see the relationship on cybersecurity change with the private sector during the Biden administration?
Bellekens: “Previous policies, such as the Cybersecurity State Coordinator Act (CSCA), were focusing on the cooperation between local, state, and federal governments, but failed to address the relationships with the private sector. However, with cyber attacks against the US public and private sector at an all-time high, we are likely to see more collaboration pledges to create open communication channels between the public and private sector aimed at improving critical infrastructure resilience.”
Herr: “Cloud computing security is increasingly the key driver for most organizations’ cybersecurity. Cloud cannot be taken for granted; the technology base offers myriad benefits but does not magic away risk. Policymakers in the White House, Department of Defense, and DHS have to reform their regulatory tools for cloud to make them more precise and responsive, then use them to compel more comprehensive security investment from cloud providers. The benefit of those changes—more intelligible and defensible technologies—would ripple throughout the public-private partnership.”
Herz: “Cybersecurity maturity mandates for federal contractors and SBOM requirements for critical infrastructure. The relationship may change because large, regulated entities, like banks and regional power systems, are just as terrified of their supply chains as the government is leery of state actor machinations. The Biden administration has a choice to change the relationship from a preach-and-blame tone to (post-SolarWinds) a more humble and collaborative government stance that seeks to learn vs. scold.”
Shahwan Edwards: “I think we’ll see the Biden administration more effectively engage the private sector to manage the growing role it plays in US cyber statecraft. There will be a better understanding of available policy levers and that cyberspace is not just about government anymore. Corporations engage in cyber diplomacy too and the Biden administration will try to make it work to their advantage.”
#5 Is there a cybersecurity policy that another country has implemented over the past decade that the Biden administration should adopt?
Bellekens: “The ‘European Union (EU) Cybersecurity Strategy,’ as the security of manufacturing facilities and associated technology and software supply chain are often overlooked, especially in the maritime sector. The EU cybersecurity strategy aims at making physical and digital critical entities more resilient and intends to integrate cybersecurity at the core of the supply chain.”
Herr: “It’s tough to point at places like Israel or Estonia because, relative to the United States, their size and historical relationship with whole of nation risk are radically different. One place the United States could take a page from is the newly single-and-ready-to-mingle United Kingdom, where the National Cyber Security Centre has been able to take an operational role alongside and, at times nudging, industry to improve the security of the UK government and core public networks. Key takeaways: invest senior executive authority in genuine technical expertise, don’t be afraid to ruffle industry feathers where necessary, and start small. Achievable goals and an end to moonshot thinking will carry this day.”
Herz: “YES. Learn from Estonia.”
Shahwan Edwards: “The Biden administration will still need to get serious about addressing the US cyber skills shortage but a reservist program like Estonia or Lithuania’s may prove helpful. That’s not to say cyber reservists will solve all our problems, but they may be useful during a time of great need, allowing the US government to surge during a cyber incident.”
Simon Handler is the assistant director of the Atlantic Council’s Cyber Statecraft Initiative under the Scowcroft Center for Strategy and Security, focused on the nexus of geopolitics and international security with cyberspace. He is a former special assistant in the United States Senate. Follow him on Twitter @SimonPHandler.

The Atlantic Council’s Cyber Statecraft Initiative, part of the Atlantic Council Technology Programs, works at the nexus of geopolitics and cybersecurity to craft strategies to help shape the conduct of statecraft and to better inform and secure users of technology.