A system of systems: Cooperation on maritime cybersecurity
Table of contents
A “system of systems”: Understanding the MTS
The MTS is a markedly complex “system of systems.” This report segments the MTS into three discrete systems—ships, ports, and cargo—each with its own life cycle. In this context, a life cycle is an analysis of the progression of a specific unit or system within the maritime transportation system. This section discusses each of these system’s interactions, processes, systems, and vulnerabilities. These three systems do not capture the entirety of the MTS, but they embody the entities most central to the sector and its security. This report seeks to highlight areas of risk and leverage for policy makers and the industry. The goal of this section is to illustrate the complexity and diversity of these core systems and expose potential points of leverage for policy change in each. Not all actors, problems, and processes fall neatly into these systems, while others are elements in every system.
Before focusing on these life cycles, it is important to identify where the sources of systemic cyber risk exist in the MTS. Although these risks manifest themselves in different ways for the distinct subsystems of the MTS, they are all proven concentrations of cyber risk that one must consider when trying to protect the MTS from cyber threats.
In the late 2000s, the public and private sectors quickly adapted security postures to address the threat posed by modern-day piracy. Years after addressing the threat, the security measures implemented then remain permanent fixtures of ships. This example demonstrates the maritime industry’s adeptness in reactively responding to crises, though it strongly contrasts with the industry’s lack of proactive behavior in addressing emerging cyber threats. There is a disconnect between the MTS and the myriad potential cybersecurity threats it faces from a gamut of criminal enterprises and states. Every misconfigured device or user-restrictive system creates a new vulnerability that opportunistic threat actors can exploit. This section aims to highlight some of the most common and consequential sources of systemic risks in the MTS.
There are two key categories of systemic risk for the MTS: human risk and systems risk. The intent of this section is to specifically highlight that vulnerabilities in technology are an important risk factor in the MTS, but the human element—and the inherent risk associated with humans working with complex and challenging-to-understand technical systems—is just as critical.
Human cyber risk
It is a common mantra in security that humans are the weakest link in the defensive chain. However, humans are also essential to any solution. A large number of cybersecurity papers,1Lance Spitzner, “This Is Why the Human Is the Weakest Link,” Information Security Training, SANS Institute blog, January 1, 2021, https://www.sans.org/blog/this-is-why-the-human-is-the-weakest-link/. conference presentations,2Alan Shimel, “CISO Talk: The Human Side of Cybersecurity,” Security Boulevard, a unit of MediaOps, February 17, 2021, https://securityboulevard.com/2021/02/ciso-talk-the-human-side-of-cybersecurity/. and corporate studies focus on this dichotomy—so much so that the human weak link is sometimes accepted as an unalterable fact.3Bob Kress, “Why Humans Are Still Security’s Weakest Link,” Accenture blog, August 31, 2020, https://www.accenture.com/us-en/blogs/security/humans-still-securitys-weakest-link.
The cliché clearly implies that the user is the weakest link in cybersecurity with no mention of the designer of the critical IT and OT systems. This seems to suggest that there is perfect information security—computers with locked down operating systems (OS), resilient applications software, secure communications protocols, and strong encryption—that can withstand any attack, until a human user enters the picture. This is not an accurate description of computer systems. No OS is completely secure, because no developer can patch all known vulnerabilities during every patch cycle, much less those yet unknown; hence the large arsenal of zero-day exploits in the wild just waiting to be launched. Software undergoes a frequent update and patch cycle. This makes the uniform distribution of the latest “up-to-date version” difficult within a large enterprise system. A communications protocol might be secure on paper, but then suffer from flaws in implementation. Indeed, many of these depend upon encryption schemes that are mathematically solid, but then weakened due to flaws in the software implementation or mismanaged keys. These vulnerabilities are not user created; they are intrinsic to any system designed and run by humans.
This becomes even more challenging with a complex ecosystem like the MTS. Ships and ports are often operating with rotating crews that may not be fully familiar with their vessels, systems, and established cyber-hygiene practices. Furthermore, crews may have varying levels of cyber literacy. A lack of digital culture and cyber literacy may benefit an attacker’s ability to gain information on a vessel and its systems or disrupt the vessel’s operations. More than anything, there is a critical need in the MTS to better understand the problems facing the sector. The easiest way to do this is more cybersecurity training, education, and certification for the MTS and its operators.
For the purposes of this report, human cyber risk in the MTS divides into four discrete categories: social engineering, lack of cyber hygiene, unauthorized access, and overcomplicated technology.
Social engineering
As discussed above, humans are the most valuable, but also the most vulnerable aspect in maritime cybersecurity, because they are the ones operating critical systems.4Oliver Fitton et al., The Future of Maritime Cyber Security, Lancaster University, n.d., https://eprints.lancs.ac.uk/id/eprint/72696/1/Cyber_Operations_in_the_Maritime_Environment_v2.0.pdf. Social engineering—or the manipulation of people—is one of the most common cyberattack vectors. Social-engineering methods include baiting, email, voicemail, and SMS phishing (and its variants), malicious email attachments, and pretexting, as well as simple deception.5“What Is Social Engineering: Attack Techniques and Prevention Methods,” Imperva Inc. website, December 29, 2019, https://www.imperva.com/learn/application-security/social-engineering-attack/. These techniques can be used by attackers to manipulate people into letting them gain access to personal computers of crew members or operators in the hopes of infecting maritime systems.
Imagine an oil tanker chosen as a target by a hacking group. In today’s society, writes a chief officer working on commercial vessels, “information regarding the vessel’s static and dynamic (course/speed/position) data, crew composition, type and quantity of cargo, destination, captain’s name, and other items of interest could be collected from the web.”6Leonid Vashchenko, “Digital Perils: Socially Engineered Attacks in Maritime Cybersecurity,” Opinion, Maritime Executive, March 5, 2021, https://www.maritime-executive.com/editorials/digital-perils-socially-engineered-attacks-in-maritime-cybersecurity. Attackers could search and exploit the social media networks of crew members, preferably the targeted vessel’s bridge team members, for additional information and deploy a spear-phishing campaign to harvest administrator-level credentials. Social media networks and websites focused on professional groups and employment make these tasks easier. With that access, the tanker’s network would be within relatively easy grasp of the hacking group.
Ships are direct targets of many of these attacks. In May 2019, the United States Coast Guard (USCG) issued a Marine Safety Information Bulletin (MSIB) specifically warning commercial vessels about targeted cyberattacks where malicious actors, using email addresses that appeared to be from a Port State Control authority, sought sensitive information such as crew members’ names, personally identifiable information (PII) and protected health information (PHI), many times under the guise of COVID-19 management.7US Coast Guard, “Cyber Adversaries Targeting Commercial Vessels,” May 24, 2019, https://www.dco.uscg.mil/Portals/9/DCO Documents/5p/MSIB/2019/MSIB_004_19.pdf.
Holland America Line and Princess Cruises—both subsidiaries of Carnival Corporation—were victimized by a phishing campaign in May 2019, although it was not announced until March 2020.8Megan Leonhardt, “Princess Cruises and Holland America Data Hacks ‘Create Extraordinary Levels of Risk’—Here’s What to Do If You Were Affected,” CNBC, March 5, 2020, https://www.cnbc.com/2020/03/05/how-to-protect-yourself-from-princess-cruise-and-holland-america-data-hack.html. The adversary sent phishing emails to employees to gain access to employee email accounts, where it was able to reap employee and customer PII, including names, Social Security numbers, other government identification numbers, passport information, credit card and financial information, and PHI, according to the report.
Ships and shipping lines are not the only potential targets. Bunker companies, fuel suppliers, shipping management companies, port operators, shipbuilders, and charterer companies could all be targeted and defrauded via email-based social-engineering attacks.
Lack of cyber hygiene
Lack of basic cybersecurity best practices, or cyber hygiene , is a critical driver of risk for the MTS. Ship crew or port operators might not be aware of the risks of downloading files from the Internet, not enabling multifactor identification, clicking on email links, or the lack of anti-virus software and firewalls on their computers. An attacker may attempt to take advantage of a crew’s lack of cyber awareness and hygiene by sending phishing emails to its members. Segregation between the crew network and the bridge network may erode during an attack, creating more problems. Anecdotes abound about poor cyber hygiene, including bridge crews implementing differentiated password controls only to post the new passwords on sticky notes. Such insecure practices highlight the challenges within the MTS when it comes to cyber awareness and hygiene.
With such enormous variation in missions and environments, ship and port managers often operate with rotating crews that may not be fully familiar with the port or vessel, its systems, and inherently the cybersecurity measures, or cyber hygiene standards, that accompany them.
Poor password practices are legion throughout the ICT-user community, and the maritime sector is no different. In August 2015, a white hat hacker reported on the ability to eavesdrop on Globalstar satellite communications systems that were both unencrypted and employing default passwords; these Internet-connected devices could be found using the Censys or Shodan search engine.9Patrick Tucker, “Hacker Cracks Satellite Communications Network,” Defense One, August 6, 2015, https://www.defenseone.com/technology/2015/08/hacker-cracks-satellite-communications-network/118915/. In October 2017, another white hat hacker detailed how SAILOR 900 VSAT systems—one of the market leaders for maritime telecommunications—around the world continued to use default passwords that could be found on Censys or Shodan as well.10Ken Munro, “OSINT from Ship Satcoms,” PenTestPartners blog, October 13, 2017, https://www.pentestpartners.com/security-blog/osint-from-ship-satcoms/. In October 2018, a 19-gigabyte Navionics database, which contains details on more than 260,000 customers, was found unsecured online due to a misconfigured database that had no password.11Charlie Osborne, “Garmin’s Navionics Exposed Data Belonging to Thousands of Customers,” ZDNet, October 9, 2018, https://www.zdnet.com/article/garmins-navionics-exposed-data-belonging-to-thousands-of-boat-owners/. These are just a few examples of how the prevalence of poor cyber hygiene can hamstring efforts for increased cybersecurity in the maritime domain.
Unauthorized access
Ships and ports are expansive and notoriously difficult to keep protected at all times. With multiple organizations, contractors, and entities working together on each ship and at each port, keeping strict oversight of access control levers can be difficult. This can manifest itself in two main ways. The first is the insider threat. Whether the individual has a personal vendetta or is bowing to manipulation by another actor through blackmail or monetary incentives, insider threats are an important threat vector. An insider attacker with intimate knowledge may be able to physically bypass access controls and restricted parts of buildings containing critical IT and OT systems, either using their own credentials or leveraging their knowledge of the port and its systems. For example, an insider attacker could gain access to a command-and-control room and place key loggers at the back of computers using a simple USB stick,12Fitton et al., The Future of Maritime Cyber Security. allowing them to retrieve desired information on port systems, including logins and passwords. A 2018 report highlighted at least two instances of abused access to deploy USB thumb drives with malware onto maritime systems.13Catalin Cimpanu, “Ships Infected with Ransomware, USB Malware, Worms,” ZDNet, December 12, 2018, https://www.zdnet.com/article/ships-infected-with-ransomware-usb-malware-worms/. These actions can result in serious, long-term consequences.
The second primary manner of obtaining unauthorized access is through linking secure and essential systems to insecure systems. Wireless networks have become the norm for web surfing and day-to-day operations in many industries across the globe. However, these networks, given their expanded use by the MTS, are attractive targets for attackers to connect to essential systems in a port or on a vessel and potentially cause significant damage.
Overcomplicated technology
In recent years, the maritime industry has pushed aggressively for technological integration, more automation, and new and improved systems. Although some new systems make sailors’ lives easier and more efficient, changes can create significant new security problems. A dearth of qualified technical know-how onboard ships exacerbates technological complexity, but it is not the source of the problem.
In 2019, the USS John S. McCain collided with the Liberian-flagged oil tanker Alnic MC.14T. Christian Miller et al., “Collision Course,” ProPublica, December 20, 2019, https://features.propublica.org/navy-uss-mccain-crash/navy-installed-touch-screen-steering-ten-sailors-paid-with-their-lives/. After an extensive review of the incident, investigators determined that an overly complicated touch-screen steering system and inadequate training were major contributors to the collision. The McCain helmsman said, “There was actually a lot of functions on there that I had no clue what on earth they did.” Afterward, a report by the National Transportation Safety Board (NTSB) said, “the design of the John S. McCain’s touch-screen steering and thrust control system increased the likelihood of the operator errors that led to the collision.”15“Collision between US Navy Destroyer John S McCain and Tanker Alnic MC, Singapore Strait, 5 Miles Northeast of Horsburgh Lighthouse, August 21, 2017,” National Transportation Safety Board, Report Adopted June 19, 2019, https://www.ntsb.gov/investigations/AccidentReports/Reports/MAR1901.pdf. This example calls attention to the potential risk of increasingly common overcomplicated technologies in the MTS.
Systems cyber risk
The MTS is comprosed of heterogeneous, complex, and often legacy systems. Maritime systems are in a constant state of evolution. Assets are highly interconnected, include both stationary (e.g., land-based) and mobile (e.g., shipboard) infrastructures, and, in many cases, remain in almost constant use. Both fixed and mobile infrastructures are interdependent and interlaced. At their core, they are driven by processes and tools such as data flows, OT systems, OT end devices, ICT systems, ICT end devices, cloud infrastructures, networked nodes, communication systems, and safety and security systems. This profusion of systems and components ranges from generic IT and OT devices to more niche elements that are specific to the maritime ecosystem. Out of all these potential attack vectors, four stand out in terms of vulnerability, volume of exploitation, and consequence.
Attacks on OT systems
The use of OT—where embedded computers directly control hardware—throughout ports and ships enables smart maritime systems. OT also includes supervisory control and data acquisition (SCADA) systems, such as flow computers, transport and transfer systems, and monitoring meters, which play a crucial role in the global transportation of oil and natural gas. The technology to support the evolution to smart maritime systems is readily available and being rapidly implemented in ports around the world.
Cybersecurity protections, however, continue to lag behind the pace of technological innovation and implementation. Although attacks on OT systems are still relatively new, cyberattacks targeting OT systems in the maritime domain have increased by 900 percent in the last three years.16“Maritime Cyber Attacks Increase By 900%,” Hellenic Shipping News. Uncovered in 2010, the Stuxnet worm targeted Siemens software that managed programmable logic controllers (PLCs) for centrifuges known for their use in Iranian nuclear research facilities. Upon infection, the controlling software would indicate normal operations on the display panel, all the while instructing the centrifuges to spin at their maximum speed and causing them to self-destruct. Stuxnetwas the first highly publicized software attack on hardware. Since then, ICS-specific attack tools have proliferated and are readily available on the Internet.17Jeffrey Ashcraft, “Monitoring ICS Cyber Operation Tools and Software Exploit Modules to Anticipate Future Threats,” FireEye blog, March 23, 2020, https://www.fireeye.com/blog/threat-research/2020/03/monitoring-ics-cyber-operation-tools-and-software-exploit-modules.html. The Stuxnetexample also proves how an attacker can exploit a vulnerability in the OT infrastructure or SCADA systems that could lead to financial or human losses.
These effects can become even more drastic within the energy sector. In August 2017, Saudi Aramco and Qatar’s RasGas were repeat victims of the 2012 Shamoon virus that crashed 30,000 personal computers and nearly reached into OT networks, with the goal of triggering an explosion.18Nicole Perlroth and Clifford Krauss, “A Cyberattack in Saudi Arabia Had a Deadly Goal. Experts Fear Another Try,” New York Times, March 15, 2018, https://www.nytimes.com/2018/03/15/technology/saudi-arabia-hacks-cyberattacks.html. The Triton/Trisis malware, first found in the wild in 2018, specifically targeted OT systems and ICS at a Saudi ONG facility. Attacks at energy facilities have the potential to cause physical effects such as explosions, threatening human life and extensive financial harm. Such an attack at a high-volume port could be devastating.
Attacks on IT systems
Wireless networks dominate day-to-day operations in many industries across the globe, and problems surrounding IT system vulnerabilities are common knowledge. However, reports assessing the security of the maritime industry indicate that open networks and weak encryption networks using the defunct Wired Equivalent Privacy (WEP), or other weak cryptography algorithms, are still in use for Wi-Fi and Internet of Things (IoT) devices in the maritime domain. Such poor network security could expose essential systems in a port or on a vessel to attackers.
The maritime industry’s digital transformation has led to widespread cloud adoption to manage personnel information, enterprise resource planning (ERP), customer relationship management (CRM), and other corporate functions. However, lack of cloud security architecture and strategy may lead to misconfigurations and unprotected application programming interfaces (APIs) that can be exploited by attackers to retrieve and collect key data. The SolarWinds supply-chain attack, publicly disclosed in late 2020, demonstrated the frailties of the software supply chain and the linchpin cloud technologies, as well as the exploitable interconnectedness of a system like the MTS.
Attacks on PNT systems
Ships rely on numerous ship-to-shore communication systems, geopositioning systems, and navigation systems to operate effectively while underway and when entering and exiting ports. Attackers could jam geopositioning systems and ship-to-shore communications, or spoof the communications to threaten the safe navigation of vessels.19Sean McCrystal, “Detecting and Defeating GPS Jamming,” Maritime Executive, February 16, 2020, https://www.maritime-executive.com/blog/detecting-and-defeating-gps-jamming. These techniques could also be used to gain a tactical advantage in a conflict.
Jamming and spoofing are far from hypothetical. GPS and AIS jamming and spoofing are problems that have been widely documented for many years,20“Understanding GPS Spoofing in Shipping: How to Stay Protected,” Safety4Sea, January 31, 2020, https://safety4sea.com/cm-understanding-gps-spoofing-in-shipping-how-to-stay-protected/. and issues related to loss in signal, or even a small positioning error, can be magnified within the relatively confined space of a port, particularly when involving increasingly large cargo and passenger ships. In 2019, the nonprofit Center for Advanced Defense Studies (C4ADS) released a report detailing Russian use of GPS spoofing to achieve a variety of disruptive and strategic objectives.21“Russian GPS Spoofing Threatens Safety of Navigation, Report Says,” Safety4Sea, April 8, 2019, https://safety4sea.com/russian-gps-spoofing-threatens-safety-of-navigation-report-says/. Additionally, AIS is among the most critical systems in the maritime industry, as it allows for the exchange of vessel positioning and information alerts, yet it was shown to be systemically insecure as early as 2013.22Marco Balduzzi et al., “Hey Captain, Where’s Your Ship? Attacking Vessel Tracking Systems for Fun and Profit,” Eleventh Annual Hack in the Box (HITB) Security Conference in Aisa, October 2013, http://conference.hitb.org/hitbsecconf2013kul/materials/D1T1%20-%20Marco%20Balduzzi,%20Kyle%20Wilhoit%20Alessandro%20Pasta%20-%20Attacking%20Vessel%20Tracking%20Systems%20for%20Fun%20and%20Profit.pdf. The potential effects of compromised PNT are significant, as modern ships rely heavily on these satellite- and radio-based systems for navigation.
Ransomware
Although it is not a specifically targeted system like the previous three categories, ransomware represents a threat to all types of systems in the MTS.23Cimpanu, “All Four of the World’s Largest Shipping Companies.” According to the US Cybersecurity and Infrastructure Security Agency (CISA), ransomware is an “ever-evolving form of malware designed to encrypt files on a device, rendering any files and the systems that rely on them unusable. Malicious actors then demand ransom in exchange for decryption.”24“Ransomware Guidance and Resources,” Cybersecurity and Infrastructure Security Agency (CISA), accessed May 4, 2021, https://www.cisa.gov/ransomware. CISA is an independent federal agency that is an operational component of the US Department of Homeland Security). Ransomware groups force companies to pay a ransom to regain control of their systems and/or to prevent the leakage of large quantities of data.
Ransomware has targeted the maritime industry in the past several years, as it has many other industries globally. The trend began in earnest in 2017, when the NotPetya operation took Maersk (and hundreds of other organziations around the world) offline, as discussed above.25Cimpanu, “All Four of the World’s Largest Shipping Companies.” In 2018, COSCO’s North American subsidiary, COSCO Shipping Lines, was hit by ransomware, shutting down its operations and IT systems for days. In 2019, hackers used the Ryuk ransomware to disrupt the entire IT network of the port, as well as several ICS systems used to transport and monitor cargo, for roughly thirty hours, completely halting operations.26Jeff Stone, “Coast Guard Says Ryuk Ransomware Hit Systems That Monitor Cargo Transfers at Maritime Facility,” CyberScoop, December 30, 2019, https://www.cyberscoop.com/ryuk-coast-guard-ransomware/. 2020 was a wake-up call for the maritime industry about the harms of ransomware, as Carnival, CMA CGM Group, Garmin, Hurtigruten, Port of Kennewick, and Toll Group were all victims of ransomware attacks.27Cimpanu, “All Four of the World’s Largest Shipping Companies.” The interconnected nature of supply chains and the differentiated actor set in the MTS make the industry especially vulnerable to ransomware and more likely to pay off ransoms in order to avoid sustained disruption of these supply chains. To help mitigate the ransomware threat to the MTS, shipping and logistics companies must improve IT hygiene and email security to harden networks against common ransomware tactics.28Danny Palmer, “Ransomware’s Perfect Target: Why One Industry Needs to Improve Cybersecurity, before It’s Too Late,” ZDNet, April 23, 2021, https://www.zdnet.com/google-amp/article/ransomwares-perfect-target-why-one-industry-needs-to-improve-cybersecurity-before-its-too-late/; and “Supply Chain Disruptions and Cyber Security in the Logistics Industry,” BlueVoyant, April 22, 2021, https://resources.bluevoyant.com/hubfs/2021 Resources/BlueVoyant – Supply Chain Disruptions and Cybersecurity in Logistics – FINAL.pdf.
Maritime life cycles
It would be impossible to individually address each subsystem in the MTS in one go. This report focuses on three key subsystems: ships, ports, and cargo. While all ports have similarities, they also are different in terms of their ownership and tenant models, cargo- and passenger-handling capabilities, mix of civilian and military vessels, jurisdictional authorities, and more. Similarly, all ships have some common functions but are different in terms of their intended purpose, operation, design, crew requirements, and regulatory practices, among other things. The life cycle for the transportation of cargo is even more differentiated (as are the key systems relied upon), depending on what type of good is being transported. The approaches to building a cyber defense within the MTS must be as varied as the elemental components within it.
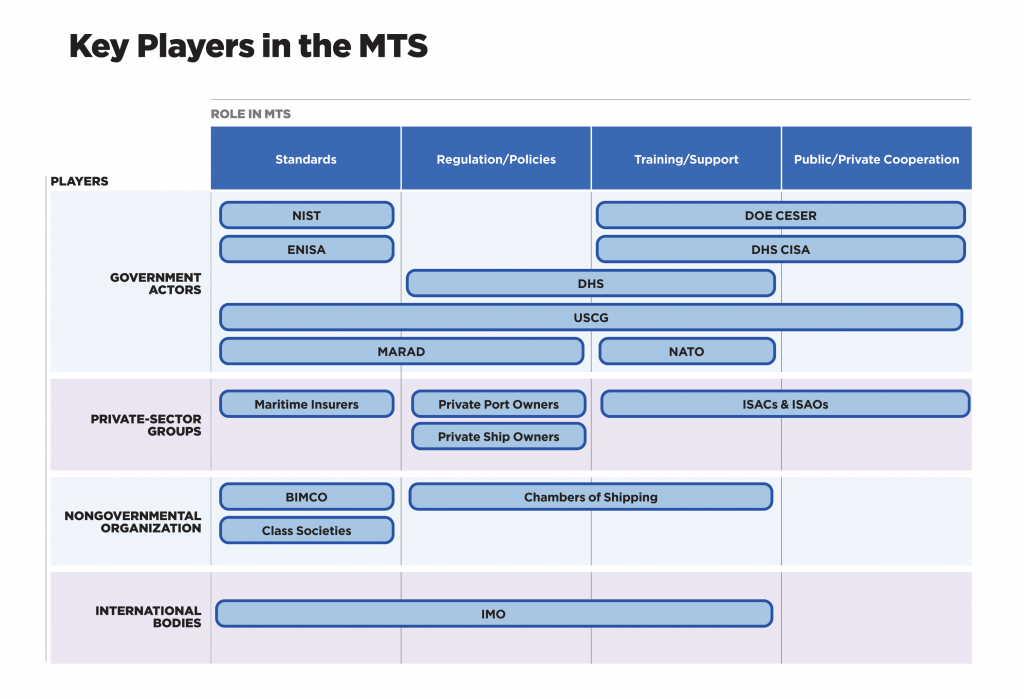
In addition to the different subsystems in the MTS, there also are a wide variety of players that are essential to the operation and security of the global MTS. As with the subsystems, it would be extremely challenging to address all of them; instead, the table below maps their roles and responsibilities. For more information on specific players, please see Appendix 1.
The following sections examine three different segments of the MTS—ships, ports, and cargo—to demonstrate the interconnectedness of the system of systems that comprises the MTS. These three subsystems of the MTS are both the most critical and the most encompassing. Each section highlights some of the key processes and cyber risks involved—and identifies points of existing programs and relationships that can be leveraged and capitalized on to better secure the MTS.
Cybersecurity and the life cycle of a ship
Ships are the heart of the maritime industry. By most historical accounts, the trading heritage of modern ocean-going vessels can be linked to the Austronesian peoples as far back as 1000 BCE.29Karan Chopra, “The History of Ships: Ancient Maritime World,” Marine Insight, September 10, 2020, https://www.marineinsight.com/maritime-history/the-history-of-ships-ancient-maritime-world/. Today, ships handle about 80 percent of global trade by volume and more than 61 percent of liquid energy trade.30“Review of Maritime Transport 2018,” UNCTAD; and “World Oil Transit Chokepoints,” EIA. They also play a key role in US national security and power projection. To address this increased demand, the evolution of ships and shipping over the ages has changed dramatically in terms of the scope of ocean-going travel, international laws and regulations, an understanding of the sea and weather, navigational methods and technologies, ship design, and so much more.
This evolution also has driven innovation in ship-based systems and their associated cyber risk due to growing technology integration and remote access by vessel shoreside management, vendors, and other essential third parties. Ships illustrate the challenge of securely designing, developing, and operating a fully connected environment—even more so when these environments look different from ship to ship. Distinct functions require specific IT and OT systems, meaning that securing each ship looks inherently different.
Protecting ships needs to be a priority. All the entities involved in the life cycle of a ship—from the designer and builder to the operator and cargo company—are susceptible to cyber threats and thus partner in this security. This section unpacks the nuances of a ship’s life cycle with respect to cybersecurity by walking through how ships are designed, constructed, operated, maintained, and decommissioned. Each section highlights some of the key processes, players, and cyber risks involved, and identifies points of existing leverage that key actors can capitalize on to better secure the MTS.
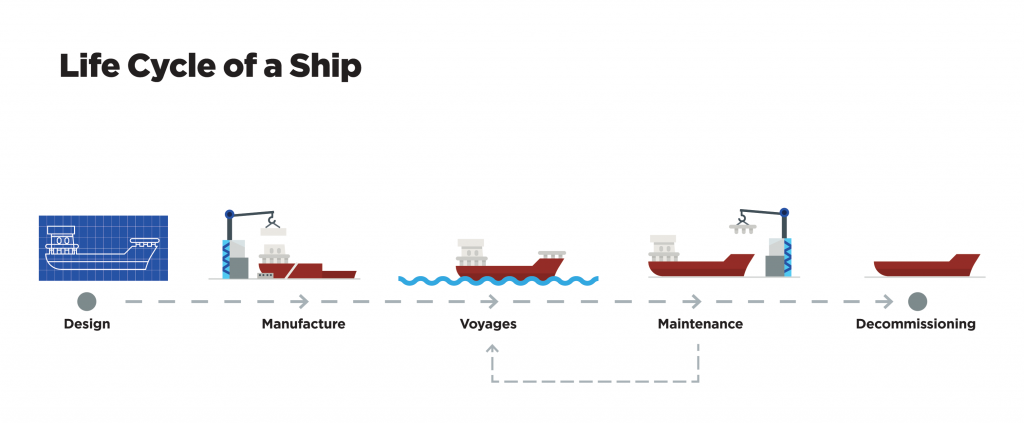
Design phase
While the primary focus of a ship’s design is related to seaworthiness and operational functionality, it is only in the last one hundred years or less that ship designers have had to address nonmaritime shipboard technologies, such as those shown below:
- Networks for intravessel communications and control, including everything from security, engineering, operations, and entertainment to cargo handling, ballast, intercoms, and integrated bridge systems; and note that cabling systems are directly impacted by the choice of communications devices and their protocols, affecting some aspects of ship design
- External communications networks for navigation, situational awareness, email, entertainment, radar, weather, and satellite phones, among other things
- ICS and OT equipment for vessel and cargo management, such as LNG transport
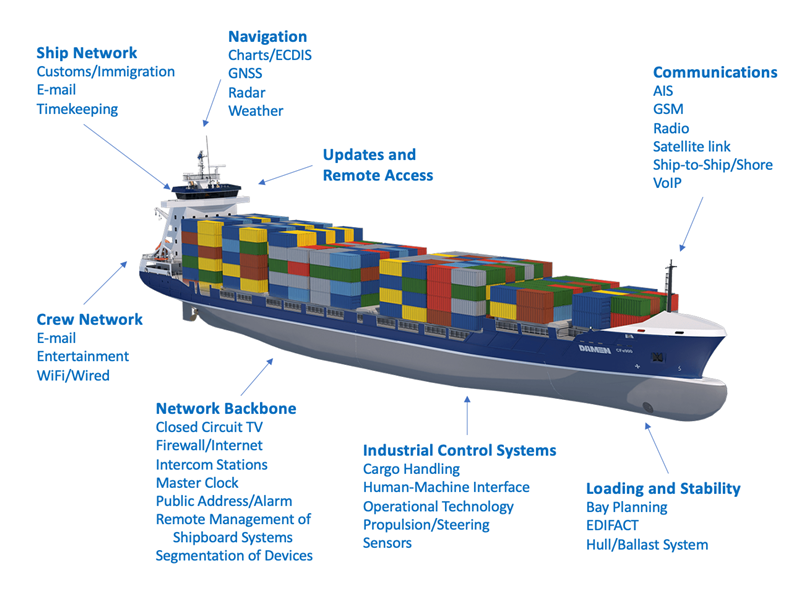
These new systems are essential for operation—yet they also must be designed and integrated securely. The computer and telecommunications networks, for example, do not merely need communication media laid out over the ship, but need to be designed and segmented in a secure fashion, necessitating cable layouts that support the secure design. Cybersecurity flaws and weaknesses introduced during the design phase and found during the shipbuilding phase will be harder and more expensive to fix.
Technical standards for the design of ships are maintained by the classification, or class, societies, nongovernmental organizations that set and maintain technical standards related to the design, construction, and operation of ships and offshore structures. These standards normally focus on elements of the ship such as the ship’s hull, propulsion and steering systems, power generation, and other systems related to a vessel’s operation. However, these standards lag when it comes to the cybersecurity of not only these core systems but also the on-board IT and ICS systems. Securely designing every aspect of a ship and its systems is a complicated endeavor, and it looks different for every ship due to factors such as size and purpose. Certain organizations like the International Maritime Organization (IMO), the Baltic and International Maritime Council (BIMCO), and the European Union Agency for Cybersecurity (ENISA), as well as the National Institute of Standards and Technology (NIST) Cybersecurity Framework, put forward guidelines on best practices when it comes to cybersecurity; by choosing not to be prescriptive, however, they have remained too wide-reaching to implement on a sector-to-sector basis, let alone ship to ship. Private-sector entities should work with these standards organizations to make them both easier to implement and more tailored to best practices.
The human element of cybersecurity also is a potential risk vector during the design phase. IP theft is a very real problem for designers and shipbuilders. In the past, there have been numerous incidents where foreign actors were able to get their hands on critical design IP, which has put operators in compromising positions.31Kevin J. Hickey et al., “Intellectual Property Violations and China: Legal Remedies,” Congressional Research Service, Report Prepared for the Members and Committees of the US Congress, R46532, https://fas.org/sgp/crs/row/R46532.pdf. Adversaries having intimate knowledge of ship design, connectivity, and the inner workings of critical ship systems makes defense tough, if not impossible. An adversary with access to ship design blueprints could even insert small changes, leading to flawed or even catastrophically problematic manufacturing.
In summary, although the design phase seems relatively simplistic, it is actually the starting point for cyber risk in ship-based maritime systems. Security in design is not just for software development—and efforts are necessary to build awareness that the ships crucial to the national economy and security must also follow the principle of whole-of-life-cycle cybersecurity.
Construction phase
The construction of a ship at a shipyard is a tightly organized, complex choreography of the parts and people required to build a ship. As most commercial ships are built in shipyards located in South Korea, China, Japan, Italy, and elsewhere, the installation of equipment and initial cybersecurity is a commitment of trust between owners and builders. Even today, it remains an incredibly labor-intensive process with limited automation in the shipbuilding process; the construction of some of the largest vessels today can take up to two years. Managing specialized parts, block construction,32Block construction is the method whereby different parts of the ship are built simultaneously in different parts of the shipyard, and then brought to the main vessel to be fit into place rather than constructing the vessel all in one place, one section at a time. and the skilled labor force (e.g., electricians, carpenters, metal workers, and engineers) provides many opportunities for a cyberattack to cause huge delays and financial loss. Unauthorized modifications to the work schedule can mean that essential workers are not available when needed, causing construction delays. A cyberattacker using intelligence gleaned from the design phase could plausibly manipulate the ordering of parts to either delay the requested arrival date or to introduce the use of counterfeit or otherwise unsound components. Extraordinary care to manage the supply chain is essential to maintain the precise timing required to get a ship built on time.

There are many ways to compromise this process. A deliberate act of sabotage or introduction of an accidental flaw during the design phase of a ship will result in a weakness in the ship’s integrity. A malign actor could introduce such a flaw and alter the design plans. A small change to a blueprint can cause one block of a ship, where block construction is employed, to fit improperly with the main vessel. This becomes a more significant problem for onboard systems and software. Imagine an insider inserting a Stuxnet-type hardware vulnerability into a critical onboard system during assembly. As the global shipping industry continues its efforts to increase automation, improve efficiency, lower costs, and adjust to an increasingly digital-driven world, there is an ever-increasing reliance on software to monitor, compute, and execute critical tasks aboard a vessel—and with this reliance comes more risk.
Additionally, the 2020 Sunburst operation has shed new light on the risks associated with software and software supply-chain compromises.33Trey Herr et al., Broken Trust: Lessons from Sunburst, Atlantic Council, March 29, 2021, https://www.atlanticcouncil.org/in-depth-research-reports/report/broken-trust-lessons-from-sunburst/. Ships rely on software to do everything from navigate to control the internal ballast systems, which often lack adequate security configuration and thus expose them on the Internet. The Sunburst campaign has shown that operations targeting these types of systems, which in this case compromised some of the biggest players in the private and public sectors, are going to become more and more the norm for sophisticated actors with nuanced strategic aims. Preventing systems entirely from these types of compromises is a fool’s errand: there simply are not enough resources in the MTS to do it. However, by better understanding the software in use and the concentration of risk on a ship, operators can better identify and mitigate potential cyberattacks as they surface. It also is important that the international maritime community, the private sector, and governments communicate extensively about these types of threats. They need to openly share attacker tactics and technical strategies for mitigation, and facilitate personnel exchanges and other forms of cross-sector and cross-national collaboration to train professionals who can understand the problems and potential threats to the MTS from a variety of perspectives. This type of multifaceted cooperation is critical to the identification and mitigation of systemic risk in the MTS.
Operations phase
A ship spends the bulk of its life at sea, going from port to port. As in the construction phase, a ship’s operation requires a complex coordination between shipping lines, ports, departments, and agencies involved in crew acquisition and management, investors, schedulers, regulators, maritime administrators, cargo handlers, fuel and ship’s stores suppliers, and more. While operating in and around US waters, ships may interact extensively with the USCG, which runs point on both law enforcement, incident response, and regulatory action for the MTS.
Supply chains are an essential linchpin to keeping a vessel on the move and operating efficiently and effectively. Ships are floating cities, complete with comparably complex computer and communications networks. A ship’s internal network interconnects with the myriad systems required to keep the vessel afloat and the external network keeps it operating efficiently at sea, as seen in figure 5. There are an estimated seventy-five to eighty thousand commercial vessels on the seas today. While ships are susceptible to nearly all kinds of cyberattacks in the operations phase, one of the biggest threats are those to navigation systems, particularly jamming and spoofing the Global Navigation Satellite System (GNSS) and v. A small error in PNT timing can cause a large error in position (e.g., one microsecond timing error can cause a vessel to be off position by 1,000 feet, or 305 m). Issues related to PNT systems have a huge potential impact on the MTS, particularly when it comes to ship operations. Attacks on navigation system can be individually disruptive by delaying a single ship’s arrival at a port or globally disruptive by causing a vessel to run aground, possibly blocking a port or waterway for days or longer. GPS spoofing has become so common in some parts of the world that many consider the system unreliable and frequently resort to navigation by other means.34Center for Advanced Defense Studies (C4ADS), Above Us Only Stars, 2019, https://www.c4reports.org/aboveusonlystars; and Todd Harrison et al., Space Threat Assessment 2020, Center for Strategic and International Studies (CSIS), 2020, https://www.csis.org/analysis/space-threat-assessment-2020. The MTS must move rapidly and aggressively to find and employ technologies to detect, combat, and mitigate the effects of AIS and GPS spoofing. In addition, the US government and DOD need to build a resilient PNT system that is resistant to attacks on satellites.35Dana A. Goward, “Assured PNT Summit–Opening Remarks,” Defense Strategies Institute Assured PNT Summit, April 14, 2021, https://rntfnd.org/2021/04/16/assured-pnt-summit-opening-remarks/.
There are multiple user levels for crew accessing shipboard IT technology. Crew members access information systems for ship operations systems specific to their job function or personal use. Ships officers have significantly more widespread usage, with higher levels of access to more systems. Senior officers have access to all ship systems, particularly those assigned to shipboard and external communications functions. The ship’s master, chief IT officer (if there is one), and possibly others, may have the responsibility to update computer systems, apply software patches, and maintain chart updates and other navigation systems. This approach is in line with normal cybersecurity practices around minimum necessary access; however, these varied levels of access can create their own problems. Depending on the level of access to these systems, an insider attacker with intimate knowledge of the security protocols could physically bypass access controls to access restricted areas containing critical systems. Compromises of IT systems can also come off as less significant than they actually are, which can lead to ship operators opting to not disclose an incident. It is essential to define what qualifies as a maritime cyber incident and set protocols to inform the proper public- and private-sector actors, namely the USCG and potential ports of call, that an incident has occurred. In recent years, the US Coast Guard has made essential steps to establish strong and transparent disclosure programs. However, we must also recognize that these programs are still relatively nascent – especially when compared to other sectors like financial services – and need to be further developed and matured with time and additional resources.
Additionally, crews onboard often lack a basic understanding of cyber hygiene. Yes, secure passwords have been installed on key systems, but that is undermined if the new password is placed on a sticky note next to the system access point. Social engineering attacks, phishing, ransomware, and other incident operations that directly target users are rampant across the entirety of cyberspace, and their impact on the MTS should not be underestimated. To combat this, there is real need for added training and education. There are US programs within the Department of Energy’s (DOE) Office of Cybersecurity, Energy Security, and Emergency Response (CESER) directorate, the Department of Homeland Security (DHS), and the USCG that focus on cybersecurity. However, current and future risks require more collaborative training across the public and private sectors, and more maritime-specific cybersecurity education. Although it seems like a small step, proper education on maritime cyber threats and cyber hygiene best practices can make a serious difference when it comes to mitigating risk.
Another potential vector for harm is the transport of malware from port to port, and to other ships, by an infected vessel. A 2019 simulation by the Cambridge Centre for Risk Studies explored the potential impact of a computer virus carried by ships that connected to port networks.36J. Dafrron et al., Shen Attack: Cyber Risk in Asia Pacific Ports, Cambridge Centre for Risk Studies, 2019, pdf-cyrim-shen-attack-final-report-exec-summary.pdf (lloyds.com). In one worst-case scenario in the simulation, the malware effectively destroyed the cargo database at fifteen ports in China, Japan, Malaysia, Singapore, and South Korea, which would cause as much as $110 billion in damages—of which 92 percent ($101 billion) would be uninsured.
Securing these critical systems and processes during the operations phase is challenging. This presents one of the largest concentrations of risk in the MTS. Some of this risk is the result of lax security-development practices on the part of the private sector and inconsistent deployment of systems previously that have resulted in insecure and hard-to-defend systems. Standards bodies and regulators, such as NIST, USCG, and maritime insurers must work with the private sector to better understand and protect critical systems. However, it also is essential to work to streamline communication internationally on key mitigation strategies and vulnerability disclosures, and invest in better education for users so that they can better understand how to protect their own systems. One key facet of this is the rate at which disclosures are identified, made public, and addressed. In the past, found-yet-unmitigated vulnerabilities have remained unaddressed for as long as a full year due to poor responses to vulnerability disclosures from vendors. This cannot continue: the MTS must double down on a need for trust through a push for policies of speed, transparency, and openness around vulnerability disclosures.
Maintenance phase
A vessel needs to move in near constant motion to produce maximum revenue. Keeping the ship operating at high capacity demands maintenance, including:
- Routine cleaning and repairs, such as repainting the hull or accommodations, or replacing worn lines and chains, and often performed while the ship is underway or at port
- Periodic refurbishment and upgrades to ship operational systems, which can include retrofitting new OT or IT systems, and requiring a short time at a maintenance yard
- A complete overhaul and rebuild, requiring an extended stay in dry dock, for hull modification, installation of new OT or IT systems, a new superstructure, or even an entire repurposing of the vessel
Even small delays in this process can yield a significant impact. The ripple effect includes the impact of how soon a ship under maintenance can get back out to sea and when the maintenance facility is available for other vessels.
The cybersecurity threats during the maintenance phase are like the construction phase, namely, financial fraud, IP theft, hacks into the work-schedule and parts-ordering systems, and supply-chain issues. However, these threats are especially prevalent in the maintenance phase because maintenance—often conducted in foreign ports—creates an opportunity for foreign-based malicious activity.
Decommissioning phase
At the end of a vessel’s life, owners decommission and, ultimately, dismantle, them. The steel used to build a vessel—that which has value—is recycled, while the rest is discarded. Ship breakers must carefully handle any hazardous materials used in construction, such as lead-based paints or asbestos, to prevent an environmental incident. Dismantling facilities are generally near water and increasingly found in developing countries, primarily in Asia.
Cybersecurity threats in this phase are similar to those of any business. Cyberfraud is of particular concern, as money changes hands for the selling and purchasing of parts and materials. Attacks on scheduling systems and databases can cause delays in the decommissioning process or mishandling of the ship’s component pieces.
Key takeaways and points of leverage
Ships represent a concentration of cyber risk in the MTS. They possess a complicated and differentiated risk model that can be challenging to address holistically because of the diversity of missions and systems and the opacity and lack of fundamental understanding of the threats. To push toward stronger cybersecurity postures for ships, this section identifies three points of leverage that represent key first steps for this initiative.
First, clearly ships are systemically insecure: yet a one-size-fits-all approach to security standards would not help solve what is inherently a vessel-specific problem. The global fleet is not monolithic—different ship owners and operators have different missions, different onboard systems, and thus, different risks. Transnational organizations like the IMO, in close partnership with the private sector and the class societies, must continue the existing NIST Cybersecurity Framework Profiles effort to provide clearer, more differentiated guidelines on cybersecurity best practices that can be implemented for specific subsections of the larger ecosystem.
Second, there is a current lack of situational awareness and collaboration in the MTS that erodes our ability to respond to emerging threats and mitigate risk on both a sector-wide and subsystem-specific basis. It is essential that the MTS expands and clarifies existing protocols and programs to streamline and incentivize information exchange and vulnerability disclosure. Whether it be through personnel exchanges, collaborative training exercises, or other forms of cross-sector and cross-national collaboration, more teamwork is essential to push forward mitigation of systemic risk in the MTS—and it must be deeper than just information exchange.
Finally, there remains a significant need for more training across the public and private sectors, as well as more maritime-specific cybersecurity education. Proper education and training on maritime cyber threats and cyber hygiene best practices can make a serious difference when it comes to mitigating risk. The United States and its key international partners must leverage preexisting training and educational programs to invest in a mandatory program for operators so that they can better understand how to protect shipboard systems and, thus, lower the systemic risk for the MTS.
As mentioned, ships are the heart of the maritime industry. Yet, the varied nature of missions and systems sets them up for failure and makes the task of widespread adaption of cybersecurity best practices a daunting one. It is impossible to increase the security of the broader MTS without addressing this.
Cybersecurity and the life cycle of a port
Retired Admiral James Loy, a former USCG commandant, is widely credited with making the wry observation, “If you’ve seen one port, you’ve seen one port.”37Joseph Keefe, “Port Security: If You’ve Seen One Port, You’ve Seen One Port,” Maritime Logistics Professional, March 6, 2019, https://www.maritimeprofessional.com/news/port-security-seen-port-seen-343481. Ports vary widely in terms of ownership and management, the mix of civilian and military vessels and operations, the interconnection of IT systems by port operators and tenants, types and skill sets of available personnel, intermodal Transport connections, the volume and type of traffic, cargo, and passengers, types of vessels that can be accommodated, and more. That said, a port is a microcosm of all aspects of the MTS activities and processes. It is a business community, and thus it has many of the same cyber issues as any other business community. Port operators and the USCG need to focus on securing a swath of maritime-specific systems that are critical to its effective operations. This is not an easy or cheap objective. It will take a significant investment of money and human resources from the US government to achieve.
Cyberattacks on ports share some similarities to those previously discussed relating to ships and shipping lines. Attacks often target both IT and OT systems, or the users who employ or have access to these systems. These incidents include phishing, email scams, cyberfraud, social engineering, internal threats, ineffective disposal of data devices, IP theft, and physical attacks on data storage and data systems.
The primary role of a port is to provide an interface between sea and land transportation. On the maritime side, ports need to accommodate many types of ships, including cargo vessels (carrying liquid/dry bulk goods, oil and natural gas, containers, or general cargo), fishing boats, passenger and vehicle ships, and port service boats (such as tugs and pilot vessels). Each type of vessel has specific berthing and loading/unloading requirements and specific dock-facing systems—and thus, each will have different types of terminals and temporary storage facilities at the port. The sheer volume and variety of requisite systems at ports make cybersecurity challenging and resource intensive. A one-size-fits-all approach will leave systems wildly unprotected.
The port or government vessel traffic-management service plays a vital role in the smooth transit of vessels into, out of, and around the port area. The various maritime terminals on land handle cargo and passenger onloading and offloading, and the port’s storage facilities provide at least temporary storage of cargo before a ship’s arrival for loading or upon unloading. Cargo and passengers transfer to other transportation modes at the port, including automobiles, buses, trucks, railroads, inland waterway vessels, and airplanes.
Ports maintain support services for all these activities, such as berthing, cargo handling, passenger and crew accommodations, transportation within the port facility, data networking and telecommunications, and everything else needed to maintain the flow of port operations. Safety and security services are important at the port to protect personnel, passengers, and cargo, particularly in this age of ports as targets of theft, terrorism, and other hostile acts. The safety perimeter of a port is not just on land, of course, but extends out to waterways within the port’s area of operation. Cybersecurity is a key element of port security—but so too is physical security.
Finally, the port must maintain services for the various agencies and other entities that have authority over some aspects of port operations. This includes the harbormaster (or the USCG’s Captain of the Port), the port administrator, governmental organizations (such as the USCG, customs, immigration, and other border protection agencies), shipping companies, financial institutions, and unions. If military vessels have a presence at the port, a liaison between military and civilian authorities also will be present.
None of the functions described above occur in isolation. A lot of data moves around a port between the port authority, ships, ship operators, governmental agencies, cargo handlers, intermodal transfer companies, financial institutions, and more. As many cyberattacks have shown, when data stop moving, everything stops moving.
Unlike a ship that has distinctive life-cycle phases, a port is in continuous operation with many simultaneous data flows, where hubs of activities intersect with other segments of the MTS and beyond. From a cybersecurity perspective, consider these ICT segments within a port including the port perimeter, information and communications technology, industrial control systems, positioning, navigation, timing, and ships.
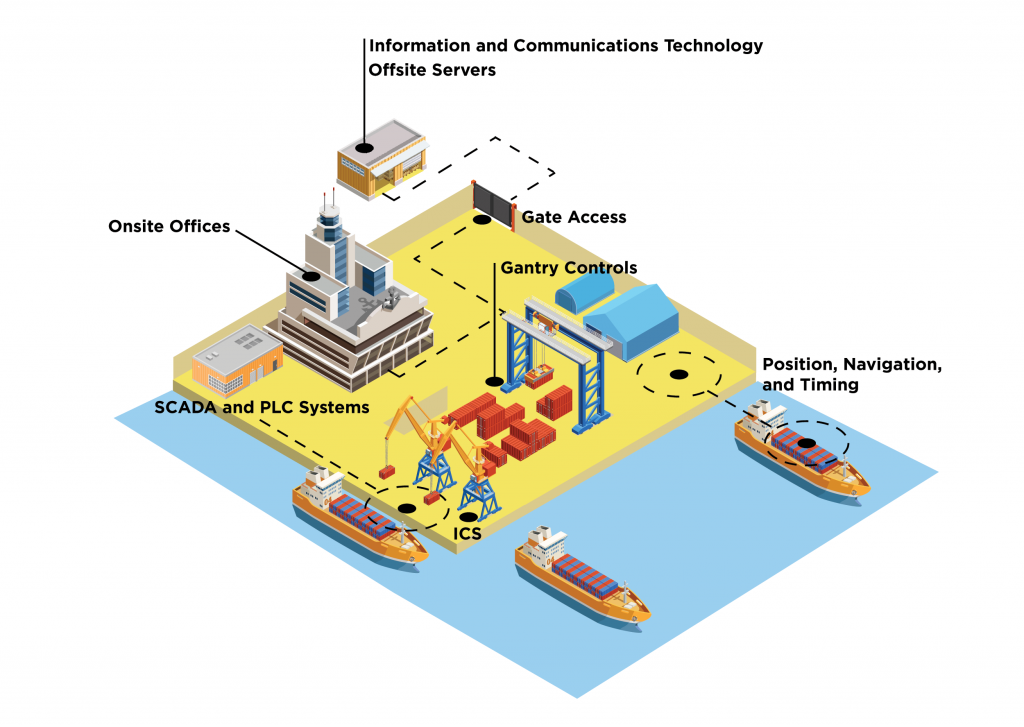
Port perimeter
The port perimeter includes all gates for ingress and egress, the secured land-based boundary, and the line depicting the water boundary of the port’s authority. The perimeter represents the first line of port security. It is at the gate and other entry points where employees, passengers, crew, contractors, vendors, and others enter and exit the port. These employees or visitors likely enter and leave in automobiles, buses, trucks, and rail cars with passengers and cargo. Motion detectors, cameras, radiation sensors, alarms, and other access-control mechanisms monitor the movement around the gates and fences, and interconnect via networks. The port’s security organization, maritime administrators, shipping agents, ship operators, immigration and customs officials, cargo handlers, logistics managers, and others must manage the movement of crew, passengers, employees, cargo, ships’ stores, and goods for the port. All these activities rely on databases and other applications that are interconnected and accessible via the Internet.
After 9/11, port management and owners were entrusted to develop and maintain security, which has been described as overwhelmingly focused on physical security. However, physical security is not just reliant on guns and guards—it also is critically dependent upon network-attached cameras, sensors, alarms, and other detection equipment. These devices connect back to a central location where security personnel can check their status. Sites such as Censys and Shodan allow anyone to search for ICS devices that are accessible via the public internet.38“Home,” Censys, March 26, 2021, https://censys.io/; and “The Search Engine for the Internet of Things,” Shodan, https://www.shodan.io/. Many documented reports of hacks on web-based cameras, vulnerable satellite communications systems, security devices, and IoT devices at ports (and on ships) have been recorded.39Tucker, “Hacker Cracks Satellite Communications Network”; and Munro, “OSINT from Ship Satcoms.” Vulnerabilities in these systems, if exploited, could easily hide an emerging physical security threat such as the access of an unapproved individual. As suggested earlier, supply-chain issues affect ports in two ways, with the port being part of the distribution side of the global supply chain as well as being a consumer. The necessary access—granted to a “trusted” business or trading partner—can circumvent both the cyber and physical defenses of a port. This is especially pertinent, because ports interact with so many contractors and independent businesses on a daily basis. Maintaining a proper perimeter and being able to monitor physical presence enable cyber and physical security—yet hinder it when breached.
Information technology (IT)
The MTS is dependent upon information and ICT, and this is possibly no truer than at a port. The organization and management of all the moving parts at a port require complex algorithms to ensure the most efficient flow of people, ships, cargo, supplies, and equipment. Machine learning (ML) and artificial intelligence (AI), coupled with ICT, are increasingly critical to modern ports, particularly as they adopt smart-port technologies.
The servers hosting information at a port manage all functions found at any business, from marketing, finance and payroll, and public relations to logistics, operations, and personnel management to ship scheduling, supply-chain management, and coordination with regulators and other authorities. All systems aspects that handle personnel files, including the immigration status of passengers and crew, are here. These systems that manage port functions are a collection of servers at the port itself, third-party services, and cloud-based services. Secure telecommunications are essential for the movement of information between all these entities.
Cyberattacks against port IT infrastructures employ the same vectors as seen elsewhere in the MTS, namely, hacks into server systems, exploitation of software, and manipulation of computer users. If a bad actor cannot break the port’s network defenses, a next step is to try to enter by posing as or compromising the network of another company that has legitimate access to the port’s network. One particularly fruitful pathway for attacks that covers all these targets is the supply chain, where ports play two significant roles. First, shipping plays an integral role in the movement of goods in the global supply chain. Second, ports themselves receive a tremendous number of products and goods for use at the port and on ships, and thus also is a consumer at the end point of global supply chains. Both roles in the supply chain create cyberattack vulnerabilities.
Industrial control systems (ICS)
Port and ship use of ICS, alongside OT, is part and parcel of the creation of the smart maritime systems of the future. Faster, smaller, and cheaper computer processors, communications networks, and sensors are enabling the Maritime IoT. ICS, coupled with AI and ML, is at the heart of the emerging automation in the MTS, including operations that are remotely controlled or remotely accessed, computer assisted, and fully autonomous. OT-based automation augments port operations with smart cranes and gantries for the onloading and offloading of cargo, digital lines, and smart ports that can check and report wind speed and direction, water temperature, depth, and other information throughout the port’s waters and berths. Autonomy is finding its way into docking systems, tugs, port vehicles, and drones. It is also essential for the energy sector; ICS is crucial for the transportation of oil and natural gas between refineries and ports, and ports and ships.

Attacks on ICS are particularly worrisome. CISA‘s Industrial Control System Joint Working Group (ICSJWG)40Industrial Control Systems Joint Working Group (ICSJWG),” Cybersecurity and Infrastructure Security Agency (CISA), https://us-cert.cisa.gov/ics/Industrial-Control-Systems-Joint-Working-Group-ICSJWG. produces a steady stream of bulletins related to attacks on the IoT infrastructure and each new vulnerability found. One of the difficulties securing many ICS devices is the minimal user interface of the embedded devices and often limited capability to alter device settings.41For example, start with the Hacked IoT database: “Hacked Internet of Things Database: Gadgets, Cameras, Wireless Routers,” Safegadget.com, August 5, 2020, https://www.safegadget.com/139/hacked-internet-things-database/.
Maritime cyber threats in this realm include attacks on the software controlling gantries and the placement of containers, both on the vessel and in the port’s staging areas. Attacks on ICS and autonomous vessels, vehicles, drones, and other systems at a port are great unknowns (e.g., autonomous docking systems and autonomous tugs), potentially altering data-gathering computers and sensors on these systems to negatively impact their operation, including causing catastrophic failures.
This is especially important for the transport of oil and natural gas. There have been several past notable cyber intrusions targeting shoreside OT energy networks including the 2017 Saudi Aramco hack,42Perlroth and Krauss, “A Cyberattack in Saudi Arabia.” and the 2018 discovery of the Triton malware.43Martin Giles, “Triton Is the World’s Most Murderous Malware, and It’s Spreading,” MIT Technology Review, March 5, 2019, https://www.technologyreview.com/2019/03/05/103328/cybersecurity-critical-infrastructure-triton-malware/. With ONG networks, the stakes start higher and only go up from there. The DOE’s CESER division has worked, often in partnership with the US national labs, on mitigation strategies for these types of operations. However, more can be done—and the private sector should play a significant role as it comprises the owners and operators of the majority of the systems in question.
The Cyber Security Agency of Singapore (CSA) offers a step in the right direction with its new Operational Technology Cybersecurity Expert Panel (OTCEP). With the inaugural meeting set for September 2021, the OTCEP will bring together a diverse and multinational group of experts on OT to strategize how to better protect these critical systems from attackers in the maritime domain.44“Establishment of Operational Technology Cybersecurity Expert Panel,” Cyber Security Agency of Singapore, May 3, 2021, https://www.csa.gov.sg/news/press-releases/establishment-of-operational-technology-cybersecurity-expert-panel. These types of initiatives should provide a road map for international collaboration on this topic going forward.
Positioning, navigation, and timing (PNT)
PNT functions are essential to the successful operation of almost all aspects of modern society. GPS and other satellite-based navigation systems offer essential positioning information for all forms of transportation, from pedestrians and bicyclists to ships and airplanes. Timing signals from GPS satellites are essential for the proper operation of all digital network infrastructures, including mobile phone and telecommunications, television, power grids, and global banking networks. GPS is also a key component to AIS, vessel traffic-management services (VTMS), scheduling and directing vessels to a berth, surveying, dredging operations, positioning of aids to navigation, chart updates, container tracking, and more.
PNT-related issues can have a huge potential impact on ports, particularly when it comes to ship operations and port management. Attacks on the navigation system could cause a ship to crash or run aground, blocking a port or waterway for days or longer. The C4ADS report indicated that the Port of Shanghai, for example, suffered undetected GPS spoofing incidents starting in 2018 and had three hundred such events occur on one day in July 2019 alone.45Mark Harris, “Ghost Ships, Crop Circles, and Soft Gold: A GPS Mystery in Shanghai,” MIT Technology Review, November 15, 2019, https://www.technologyreview.com/2019/11/15/131940/ghost-ships-crop-circles-and-soft-gold-a-gps-mystery-in-shanghai/. Maritime Safety Administration (MSA) boats are frequent targets of GPS spoofing: one was spoofed 394 times in a nine-month period.46Harris, “Ghost Ships, Crop Circles, and Soft Gold.”
AIS spoofing is another ongoing threat in port areas. Smugglers often spoof AIS signals from legitimate vessels to escape detection by the authorities. The Shanghai MSA reports that vessels carrying banned sand and gravel accounted for twenty-three collisions or allisions on the Yangtze River in 2018, with the loss of fifty-three lives.47Harris, “Ghost Ships, Crop Circles, and Soft Gold.” In 2019, a tanker suspected of smuggling oil was sending cloned AIS signals and, reportedly, rammed an MSA patrol boat to evade capture.48Harris, “Ghost Ships, Crop Circles, and Soft Gold.”
Clearly, bad actors will continue to exploit PNT systems in the coming years—yet the private sector has yet to produce a safer alternative. Without a more secure and defensible product, it is hard to image this problem diminishing.
Ships
While vessels in transit always fill ports, they also have fleets of local vessels, including pilot boats, tugs, local commercial fishing and cargo vessels, public safety and law enforcement boats, and recreational boats. As central hubs connecting with thousands of ships, relationships of mutual trust often exist. However, this trust is likely unwarranted and even dangerous, and the safest approach is a zero-trust model.
When it comes to cyber incidents in the MTS, the lack of a consistent threat matrix further justifies this safe approach. As an example, the Shen Attack report highlighted the potential for a visiting vessel to infect a port’s network and how that infection could then spread to other ships on the network.49J. Daffron et al., “Shen Attack.” The port’s network, then, becomes an amplification point in the spread of malware. To avoid this, ports must properly report and silo (or disconnect) any infected ship and its systems until resolving the compromise. However, the present lack of reporting standards leads to an erosion of the situational awareness that is essential for port law enforcement and incident responder. The MTS needs to be a step ahead of these types of threats—not a step behind. The private and public sectors need to work together to clarify incident reporting standards. Ensuring that key actors are aware of a potential breach helps address compromised systems accordingly and contain the spread.
Key takeaways and points of leverage
Ships are critical to the MTS as they are the main hub for commercial interactions in the industry; yet they existentially rely on certain sets of insecure systems to facilitate these interactions. To push toward stronger cybersecurity postures for ports and their core processes, this section identifies three points of leverage that represent key first steps.
First, the sheer volume and variety of requisite systems at ports make keeping a proper cybersecurity posture a challenging and resource-intensive goal; a one-size-fits-all approach will leave many systems unprotected. As with ships, stakeholders across the international public and private sectors must work together to set guidelines and best practices for cybersecurity risk management at ports—but this is not enough. Actors seeking to improve security in the MTS must also work directly with procurement bodies, such as the Federal Acquisition Security Council (FASC), to incentivize the design of more secure systems. If systems are insecure before they ever even become part of the MTS, ports are fighting with one hand tied behind their back. Second, port security is stuck in a post 9/11 world. In 2021, the physical security of ports and the goods stored there is not just reliant on guns and guards—it is also critically dependent upon the ability of network-attached cameras, sensors, alarms, and other intrusion detection equipment to help identify human threats. It is critical that port operators, as well as the USCG, advance an effective security mindset at ports that utilizes resources properly to secure ports from modern threats, not outdated ones. Finally, it is crucial to limit the spread of potential infections between ships and ports. The Shen report, described earlier, highlighted the potential for a visiting vessel to infect a port’s network and amplify the spread of malware,50Shen Attack: How a Virus Could Disrupt Asia-Pacific Ports Operation, Safety4Sea, November 7, 2019, https://safety4sea.com/shen-attack-how-a-virus-could-disrupt-asia-pacific-ports-operation/. which represents a systemic threat to not only a port but to the global maritime ecosystem. By strictly tiering and defining what qualifies as a significant maritime cyber incident and streamlining protocols to inform the proper public- and private-sector actors in the case of an incident, the potential risk and extreme blast radius of more sophisticated incidents can be reduced.
In summary, ports are a microcosm of the larger MTS and sit firmly at the heart of the maritime industry. One single port may interact with hundreds of ships and thousands of individuals in a single day. These challenges make cybersecurity at ports a difficult and ever-evolving situation.
Cybersecurity and the life cycle of cargo
The transport of cargo—whether it be tourists on a cruise ship, towering stacks of containers on a transoceanic transport ship, or oil and natural gas sealed inside the hull of a tanker ship—is the central purpose of the MTS. Outside of humans, ships today carry every imaginable type and combination of goods, in many form factors, including inland and near-coastal barges, container ships, bulk-goods cargo vessels, roll-on/roll-off (ro-ro) ships and ferries, oil tankers, and LNG carriers.
The volume of cargo transported, as well as the locations from which it ships to and from, is alone an expansive discussion. An interactive map, created by Kiln and University College London’s Energy Institute, illuminates the diversity in missions and destinations when it comes to the global movement of cargo in the MTS.51Will Martin, “This Amazing Visualisation Shows How the World’s Ships Move Goods around the Globe,” Business Insider, December 23, 2017, https://www.businessinsider.com/map-of-global-shipping-interactive-2017-12; the visualization also can be seen at https://www.kiln.digital/.
Matching the diversity of cargo is an ever-widening array of cyber threats facing maritime cargo transport. Many types of cyberattacks can be directed at cargo, either while it is in place or in transit. These attacks share many similarities with those on ports and ships—especially because the transportation of cargo is existentially dependent on ports and ships for transportation. Depending on the type of cargo, the types of ship- and port-based systems used for transport, and which part of the life cycle of cargo the attackers are targeting, different segments of the systemic cyber threats facing the MTS can manifest themselves as the biggest drivers of risk for cargo.
The rest of this section unpacks cargo’s life cycle in the MTS by looking at cybersecurity risks posed on commercial containers and ONG products in storage, at their originating port, at sea, and when they reach their final destination. Neither intends to provide a complete picture of the type of cargo transported throughout the MTS; instead, they serve as demonstrations of where this risk can be most concentrated.
For commercial container shipping, consider the life cycle of what’s called an intermodal container, due to its standard size and design so that it can travel by truck, rail, or ship. The twenty-foot equivalent unit (TEU) is the standard measure of a ship’s cargo-carrying capacity, and generally corresponds to a single truck or rail car.

For the transportation of ONG products, a barrel—defined as containing 42 US gallons of liquid product—are the primary unit of measurement.52“Oil and Gas Measurement Unit,” Petroleum Geology Class website, Chulalongkorn University, weebly.com. There are many systems that play a part in transporting ONG products, however, there are four that are most essential to the success of the transportation process: tank monitoring and storage systems; terminal transfer and pumping systems; loading racks; and automation control systems, instrumentation, valving, and metering. These systems enable critical processes throughout the cargo life cycle, and the sections below address them in detail where applicable.
Despite differing types of cargo, the routine of transporting either a commercial TEU or a barrel of ONG starts well before entering the MTS at one port and ends well after leaving the MTS:
- Storage (Origin)
- Port of Embarkation
- In Transit at Sea
- Port of Debarkation
- Storage (Destination)

Storage
The initial storage facility, whether it be a warehouse, tank farm, or something more niche, represents the first stop for any cargo beginning its journey through the MTS. Goods in the process of shipping need safe and secure storage to protect them from potentially damaging threats such as the elements of nature, damage and destruction due to careless handling, pilferage, etc.53Anish Wankhede, “Watch: How Container Shipping Works—The Process of Transporting Cargo in Containers,” Marine Insight, May 27, 2020, https://www.marineinsight.com/videos/watch-how-container-shipping-works-the-process-of-transporting-cargo-in-containers/. Depending on the type of cargo, these goods can often spend extended periods of time in warehouses, exposing them to a variety of threats.
Most modern storage facilities are engineering marvels that utilize large swathes of technology to facilitate key processes such as sensitive or temperature-controlled units, transport, and inventory management, among other roles. The sheer complexity of these facilities creates significant opportunity for cyberattacks during the cargo’s life cycle. This can manifest in several ways. First, there has been a significant surge in automation in storage facilities. Technology intended for manufacturing now assists with distributing assets and prepping and packing them for transport in storage facilities across the country.54Fergal Glynn, “50 Expert Warehouse Automation Tips and Best Practices,” 6 River Systems, March 18, 2021, https://6river.com/warehouse-automation-tips-and-best-practices/. Increased automation has also driven an increase in the need for collaborative and remote management tools. Some smart warehouses use drones or robots for moving and packing goods.55Hari Menon, “Guide to Types of Warehouses for Shipping,” Marine Insight, February 9, 2021, https://www.marineinsight.com/maritime-law/guide-to-types-of-warehouses-for-shipping/. Warehouses also come in many shapes and sizes.56Menon, “Guide to Types of Warehouses.” Public warehouses are government run and used by both public- and private-sector actors, while private warehouses are often owned by a shipper or a shipping line.
For TEUs, there are many cyber-enabled attacks on IT systems that can impact the shipper, shipping line, and warehouse prior to a container formally entering the MTS. As an example, financially motivated bad actors have proved capable of the electronic manipulation of both cargo documentation and handling systems.57Rosehana Amin, Rory Duncan, and Daniel Jones, “A Very Modern Form of Piracy: Cybercrime against the Shipping Industry—Part 1: Rapidly Developing Risks,” Lexology, March 23, 2021, https://www.lexology.com/library/detail.aspx?g=b4dc3b52-40b5-4700-afee-a95d09b7b6d3. Additionally, cyberfraud, financial fraud, false bills of lading (often used to cover up smuggling of illegal or contraband goods), cargo theft, and more can all happen by attacking the shipper’s data centers and IT infrastructure, and manipulating inputs such as what is supposed to go where. IP theft also is a factor at warehouses and ports, where an intruder can learn about the contents of containers, as well as the transport schedule and other information that might have value to a competitor or adversary.58Barry Hochfelder, “Cyber Pirates: The Latest Threat to Ocean Shipping,” Supply Chain Dive, April 30, 2018, https://www.supplychaindive.com/news/ocean-shipping-carriers-cyber-risk/522417/.
OT systems in storage facilities are also vulnerable to cyber exploitation. Often, perishable products, such as food that needs to be chilled, or barrels of oil and natural gas, which must be carefully transported and stored, can be held in these warehouses. Research confirms the existence of adversary capability to disrupt the types of cooling systems used to chill a container of temperamental goods, thus causing spoilage of the contents and disrupting key shipments before they have even left their initial location.59Shefali Kapadia, “3 Years, 3 Cyberattacks on Major Ocean Carriers. How Can Shippers Protect Themselves?,” Supply Chain Dive, April 29, 2020, https://www.supplychaindive.com/news/ocean-carrier-cybersecurity-maersk-msc-cosco/576754/. Although there have been limited examples of these types of attacks on storage systems in the wild, they represent a threat vector that is a risk throughout the life cycle of cargo and a potential target for adversaries in the near future.
The human element is a huge challenge for storage as well. Like ports, storage areas can be a dynamic employment environment with employees, independent contractors, and external agents (such as truckers) moving in and out all day. Imagine an overseas manufacturer or nation-state bad actor entering a shared government warehouse to place a malicious device into containers bound for a ship with which to launch a broader cyber operation against the MTS.60“Cargo Theft: A Billion-Dollar Problem,” Ship Technology, July 30, 2017, https://www.ship-technology.com/features/featurecargo-theft-a-billion-dollar-problem-5882653/. The human element of cyber risk clearly exists for warehouses and it cannot be mitigated without a better understanding of cyber hygiene and best practices.
For ONG products, the risks associated with product storage at this point in the process looks slightly different. Storage and the security of ONG cargo while at rest is a critical concern. Yet, unlike TEUs, they are rarely placed in designated warehouses. Instead, ONG products are often stored in large oil terminals at ports, which are essentially large groupings of tanks used to store oil and natural gas before it is loaded onto vessels for transport (fig. 11).

Monitoring the status of these tanks is essential to the security and financial health of the transport process. Tank monitoring systems allow users to check fluid levels in multiple tanks, across multiple sites, from a remote location—preventing users from overfilling tanks, which is not only costly but has been known to potentially lead to fires and explosions.61Dean Mallon, “Please Enable Cookies,” StackPath, February 8, 2019, https://www.piprocessinstrumentation.com/instrumentation/level-measurement/article/15564207/performing-a-storage-tank-risk-assessment. These systems will notify users when a wide variety of problems occur, including changes in volume and fluid levels—allowing owners to assess their product, no matter where it is geographically located. However, this intersection between critical safety need and remote-monitoring capabilities makes monitoring systems a potential flashpoint for cyber risk. By shutting down or manipulating the functionality of these devices, an adversary could disguise malicious activity until it is too late to stop the potentially explosive effects.
It is true that many of the potential threats discussed here, and throughout this cargo section, have yet to be directly exploited by an adversary—at least to the authors’ knowledge. However, the consequences of these potential vulnerabilities underline the fact that stakeholders in the MTS need to be looking forward, not backward. A reactionary approach to addressing cybersecurity threats will not only misallocate the limited funds for cybersecurity that do exist, but also leave operators unprepared for the tactics of ever-evolving adversaries.
Originating port
Once cargo is ready to begin its journey, it goes from the initial storage location to its port of departure via train, truck, or some other form of transportation. This process looks different for TEUs versus ONG products.
First, TEUs: after some level of inspection and verification, information about the container is entered (usually automatically) into the port’s computers. The container then gets directed to a staging area, where it stays until the proper time to be moved to the designated berth and loaded onboard a ship. A container ship typically carries hundreds or thousands of TEUs. This requires a complex set of algorithms to optimize loading and unloading sequences and exact ship locations, as well as managing the ship’s ballast. These algorithms need to determine a container’s placement based upon the entire voyage of the vessel and knowing at which stop on the trip the container will be offloaded, special requirements for the TEU (e.g., ensuring that a container is placed in a powered bay, if required), and the load balancing needs of the ship. This complexity is the root cause of insecurity at this stage. Additionally, depending on the type of cargo, the loading process looks different; nonstandard containers and other types of goods may go through a slightly different process.
The choreography of loading (and unloading) containers is a result of messages exchanged between the shipping agents, stevedores, tonnage centers, and ship’s master/cargo officer. The cybersecurity risk here can be huge. Attacks on the loading/unloading software, IP theft, cargo manifest, bayplan/stowage information, ICS/OT controllers, and more at ports can cause a misloaded vessel and harm to cargo or the ship itself, as well as other potential affects.
Attacks on ICS and OT systems can be extremely disruptive at this stage, very similar to ports, causing potential misloading or misstaging of cargo containers. A misloaded ship could be particularly vulnerable to rough seas, leading to the loss of containers overboard or other negative effects.62Kim Link-Wills, “260 Containers Lost, 65 Damaged in Maersk Eindhoven At-sea Mishap,” FreightWaves, February 19, 2021, https://www.freightwaves.com/news/260-containers-lost-65-damaged-in-maersk-eindhoven-at-sea-mishap. Such attacks can also damage or disable gantries, cranes, TEU containers, port vehicles, and vessels. The research firm Trend Micro demonstrated a comparable operation in 2019, proving the ability to take control of several large commercial cranes.63Peter Fabris, “Hackers Can Easily Take Control of Construction Cranes,” Codes and Standards content, Building Design & Construction magazine, January 23, 2019, https://www.bdcnetwork.com/hackers-can-easily-take-control-construction-cranes. Although these types of attacks have yet to widely manifest in the MTS, they represent the next step of potential exploitations in the MTS and a clear example of the physical and economic effects of a potential attack. Port owners and operators need to work closely with the US government to better understand their cyber risk profile in the MTS and begin to implement best practices that can start to reduce this system risk.
This process looks distinctly different for ONG products. Before any ship planning to transport ONG can get underway, terminal transfer-line systems must move the product from the port’s storage facilities to the shipside tanks. This collection of pumps and pipelines allow oil and natural gas to safely and directly travel from storage tanks at the port to storage tanks near the ships.
Once safely transferred shipside, the ONG product is loaded onto ships using loadout racks. This structure, located at a terminal or bulk plant, consists of a platform and a loading arm designed for use in loading the compartments of an oil-transport vessel. These automated systems actually load the cargo onto the ships themselves. Throughout this process, operators use metering systems to enable operators to monitor and manage the oil and natural gas that they are transporting to ensure the proper quality and volume. In some ways, consistent metering is one of the most crucial parts of this process, as product measurement is one of the clearest determinants of revenue for the industry and thus has a direct impact on profit.
To automate the process of tanking and loadout, these systems typically utilize automation platform technologies such as distributed control systems (DCS), safety instrumented systems (SIS), programmable logic controllers, process automation controllers (PAC), remote terminal units (TRU) and other remote input/output hardware (I/O).64Ryan Williams, “PLC vs. PAC vs. IPCs,” Control Engineering, November 16, 2015, https://www.controleng.com/articles/plc-vs-pac-vs-ipcs/. Newer technology also has allowed for wireless field instrumentation and communication mesh networks that are designed for industrial area classifications in the ONG environment. Many of these systems for the last two decades have ethernet network-based communications on the processors, workstations, and network hardware and have migrated from traditionally separated systems over the years to enterprise IT networks to be even more integrated.
Owners and operators rely on these systems when moving ONG from ports to ships. However, the past has revealed flaws and operational vulnerabilities with these crucial systems—and the risks are high. First, these critical systems can be susceptible to insecure remote-access processes, leaving them potentially vulnerable for exploitation. This is a tough problem to solve, as remote access—the ability to analyze and review the performance of systems remotely, which is essential for ONG transportation—is critical in a maritime domain when it comes to safety and maintenance. However, this connectivity also inherently broadens the attack surface for these systems. Second, like the rest of the MTS, cyber risks exist during the entirety of the transport process due to a lack of knowledge of cyber hygiene in the broader operator community. One example is the use of Wi-Fi networks by crew, both onboard and at ports, which can open new avenues for exploitation and lateral movement through social engineering attacks. Finally, so-called tech bleed overrepresents another potential threat vector for these systems. Although many critical ONG systems are designed to be secure, the evolution of ship’s technology over time can result in new levels of connectivity and greater exposure.
It is critical that the ICS systems that enable the secure transportation of ONG goods are better protected. Imagine the implications of a system disruption during fuel transfer between a ship and a port, resulting in an environmental spill, a significant explosion, and potential loss of life. The biggest problem when it comes to mitigating these cyber risks is that organizations do not know where to begin, and this applies to humans as well as systems. The NIST Cybersecurity Framework is a good start, but the MTS needs more specificity, especially when it comes to bulk energy operators. The North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) standards are a good road map and should be implemented more holistically across ports that rely on these critical systems to transport ONG products.
In transit
Once loaded up, containers and other types of cargo are then transported from the origination port to the destination port on a route that could include intermediate ports, where other containers have scheduled offloads and added cargo that needs loading.
The cybersecurity threat for cargo at sea is minimal, but not nonexistent, and it often aligns with the cyber threats discussed for ships above. A cyberattack on a cargo vessel can directly impact the cargo in transit. A refrigerated container, for example, might lose power, thus causing spoilage of the contents. Safety and monitoring devices on a bulk oil carrier might be turned off, affecting the stability of the vessel and putting lives and cargo at risk. A cyberattack on the loading/offloading systems of an LNG carrier could cause a catastrophic failure of the cooling mechanisms necessary to maintain the safe transport of the fuel. A cyberattack on the shipboard system that causes an electrical cutoff at powered bays could allow a flash-point increase near a container with flammable vapors.
A malicious actor could introduce a rogue communications device in a container to launch a cyberattack on a ship’s or port’s network. With some major liners exploring IoT-enabled containers, which customers can access remotely, the container itself may become a target vector. In most cases, ship operators do their best to ensure proper cybersecurity practices are followed, including network segmentation. However, the connectivity of these new smart containers, if accessed while onboard, could widen the attack surface for ships. This could lead to compounding effects in the operation of a ship’s navigation or communications systems or, in a worst-case scenario, connect to networks at the ports to which the ship visits—leading to even more lateral movement. Although this type of operation may be rare, it only serves to further highlight the interconnected nature of the cyber threats to the MTS.
One thing to consider during this segment of cargo transportation is the ability for a cyber operation to affect physical operations. For the maritime domain, the most obvious example is pirates. A 2016 case study known as “Roman Holiday” illuminates this risk.65Marcus Hand, “Cyberattack Allows Pirates to Target Cargo to Steal,” Seatrade Maritime News, July 7, 2016, https://www.seatrade-maritime.com/americas/cyber-attack-allows-pirates-target-cargo-steal. During this operation, pirates raided an anonymous shipping company multiple times. This is not irregular—pirates are known to raid commercial cargo transports. The outlier in this case, however, was that these pirates seemed to know exactly where the highest valued goods were on the ship without having to search for them. It was later identified that the company’s content management system—where the ship’s bills of lading lived—had been compromised. In this case, the only negative effects were stolen goods and a loss of profit. However, if you exchange the commercial goods in this scenario for, say, nuclear processing components, the potential risk of cyber-shaped physical operations becomes abundantly clear.
Destination port
Once the cargo reaches its final destination port, the trip at sea is complete and it is time to unload. The process at the destination port is like that at the originating port, but in reverse. Oil and natural gas must pass through the same chain of systems discussed above to unload. Containers to be unloaded from a vessel need to be accurately identified, and unloading algorithms control container removal and staging. The process looks slightly different depending on the cargo, but in all cases there is a critical reliance on technology to do so.
As before, messages exchanged between shipping agents, stevedores, tonnage centers, and the ship’s master/cargo officer dictate the choreography to unload the containers. Information about each container must be entered (usually automatically) into the port’s computers. Customs inspections need to be managed and bills of lading need to be reviewed and inspected.
Although the attack vectors look similar for unloading ships and loading them, the potential uses for adversaries can look distinctly different. Between 2011 and 2013, a criminal group was able to gain access to the Port of Antwerp’s IT systems.66“Antwerp Incident Highlights Maritime IT Security Risk,” Seatrade Maritime News, October 21, 2013, https://www.seatrade-maritime.com/europe/antwerp-incident-highlights-maritime-it-security-risk. They capitalized on this access by using it to identify and intercept the containers their international partners had filled with illicit drugs. When their access was eventually discovered and mitigated, the criminals physically broke into the facility and downloaded malware that allowed them to continue their operation unmonitored.67Fred S. Roberts et al., “Combined Cyber and Physical Attacks on the Maritime Transportation System,” NATO Maritime Interdiction Operational Training Centre (NMIOTC), Maritime Interdiction Operations Journal 18, no. 1 (2019): 27-37, https://nmiotc.nato.int/wp-content/uploads/2019/10/NMIOTC-18-2019-A-Internet.pdf. Not only does this illustrate how cyber and physical activity can intersect in the maritime domain, but it also shows how comparable risks to the cargo transportation process can manifest in diverse ways for malicious actors throughout the life cycle.
Ultimately, containers and other goods are placed onto appropriate intermodal Transport to be taken off-site and transported back to a shipper or warehouse. The cybersecurity threat during this stage can be significant as well. Attacks on the loading/unloading software or ICS/OT controllers can cause a shift in the balance of a vessel or harm to cargo (or the ship). Falsified or altered bills of lading can also cover up smuggling of illegal or contraband goods, or theft of cargo.
Destination storage
Once the cargo has been taken off the ship and processed at its destination port, it is time to make its way to its final destination. Full containers and other types of cargo eventually arrive at a distribution warehouse, where they are emptied, sorted, categorized, and the contents distributed to other forms of transport to their ultimate destination. ONG products are transferred from their ships into new tanker farms before they are eventually loaded onto other forms of transport and shipped to their final destinations.
The information security issues here are very broad and similar in almost every way to those discussed above. By attacking the shipper’s critical systems, bad actors can accomplish cyberfraud, financial fraud, false bills of lading (often used to cover up the smuggling of illegal or contraband goods), IP theft, exploited OT and IT systems, cargo theft, and more. Cyberfraud and financial crimes hit shippers through fake orders or money transfers directed to the warehouse, intermodal Transport companies, or the port itself. The actual theft of cargo can be directed at warehouses and ports via bogus orders, bills of lading, or shipping instructions.
Key takeaways and points of leverage
Cargo is the fuel that drives the MTS and the connective tissue between ports and ships. This means that the transportation of cargo is the main profit driver for the MTS; yet the transportation of that cargo is also reliant on the ability of operators to mitigate many of the same cyber threats facing both ports and ships. To push toward stronger cybersecurity postures for the transportation of cargo, this section identifies three points of leverage that represent key first steps.
First, the transportation of cargo is an inherently interconnected business. It cannot happen without ports, ships, and shipping companies, not to mention the owner of the cargo. Shipping companies must work with ship and port owner-operators to help them facilitate the implementation of best practices and standards, and share information to protect their bottom line.
Second, industry leaders need to stop being reactive when it comes to cyber threats and start looking forward. Just as our systems continue to evolve, so will the tactics and capabilities of our adversaries. Many of the potential cyber vulnerabilities to cargo discussed in this section have not yet been exploited by malicious actors; but waiting until they are would be a critical mistake. Key stakeholders in the MTS, including the public and private sectors and academia, must follow the example of programs like GridEx, Project Evergreen, or the United Kingdom’s Cyber-Ship Lab, and work to address these next-generation vulnerabilities before they are utilized by our enemies.68Naveen Goud, “UK Hosts £3 Million ‘Cyber Ship Lab’ to Prevent Cyber Attacks on Maritime,”Cybersecurity Insiders, November 5, 2019, https://www.cybersecurity-insiders.com/uk-hosts-3-million-cyber-ship-lab-to-prevent-cyber-attacks-on-maritime/.
Finally, there is a critical need to better protect the storage and transportation systems that are vital to the transportation of ONG products. These systems look different from others in the MTS and have potentially destructive consequences from as yet unexploited vulnerabilities. Implementing the NERC CIP standards for these systems would be a good first step—but it cannot be the last one.
In summary, cargo is not only the main economic driver of the MTS but also inherently relies upon ships and ports on a daily basis to make sure it can reach its final destination. This reliance leaves it vulnerable to a wider variety of threats.
Explore the full report
A system of systems is part of a larger body of content encompassing the entirety of Raising the colors: Signaling for cooperation on maritime cybersecurity— use the buttons below to explore this report online.
The Atlantic Council’s Cyber Statecraft Initiative, within the Scowcroft Center for Strategy and Security, works at the nexus of geopolitics and cybersecurity to craft strategies to help shape the conduct of statecraft and to better inform and secure users of technology.
Related content
Image: Freightliner cargo ship.